SSL/TLS Certificate Lifespans Are Decreasing to 200 Days
Sectigo will begin issuing 199-day certificates starting March 12, 2026. Are you ready to handle doubling certificate reissuances?
The CA/Browser Forum’s (CABF) Sunday, March 15, 2026 deadline to reduce certificate validity is nearly upon us. However, the change to 200-day validity will take effect sooner, as many certification authorities (CAs), including Sectigo, are enforcing these changes in advance to ensure a smooth transition.
When and why are these changes happening, and how will the decreased certificate validity periods affect your organization?
Industry Outlook: What’s Happening and When?
You’ve seen the headlines: Starting March 15, 2026, the industry will drop to a 200-day maximum validity period for publicly trusted SSL/TLS certificates. (The same 200-day cap also applies to IP address and domain control validation [DCV] data reuse periods.)
Don't make the same mistakes
Yahoo, Equifax, Home Depot,
LinkedIn, and Ericsson did!
Get our free 15-point checklist and
avoid the same costly pitfalls.
Contact details collected on InfoSec Insights may be used to send you requested information, blog update notices, and for marketing purposes. Learn more...
But the reality isn’t quite so straightforward: SSL/TLS certificates issued by any CA worth its salt will be valid for no longer than 199 days. This is because every digital certificate is issued with a lifespan specified down to the second (literally).
Why the Discrepancy (200 vs 199 Days)?
A certificate that’s issued with a 200-day lifespan will violate the CABF’s server certificate baseline requirements. This is because any certificate issued with a 200-day validity period is actually valid for 200 days plus one second due to how CAs’ systems work. These systems issue certificates with lifespans from midnight of day one to midnight of the last day, resulting in an extra second that is pivotal.
Check out this explanation from Sectigo’s Tim Callan and Jason Soroko:
While it may seem like we’re splitting hairs, this extra second is crucial because a certificate issued with an additional second would be considered misissued and would ultimately be revoked.
Industry Certificate Validity Period Reductions Won’t End at 200 Days
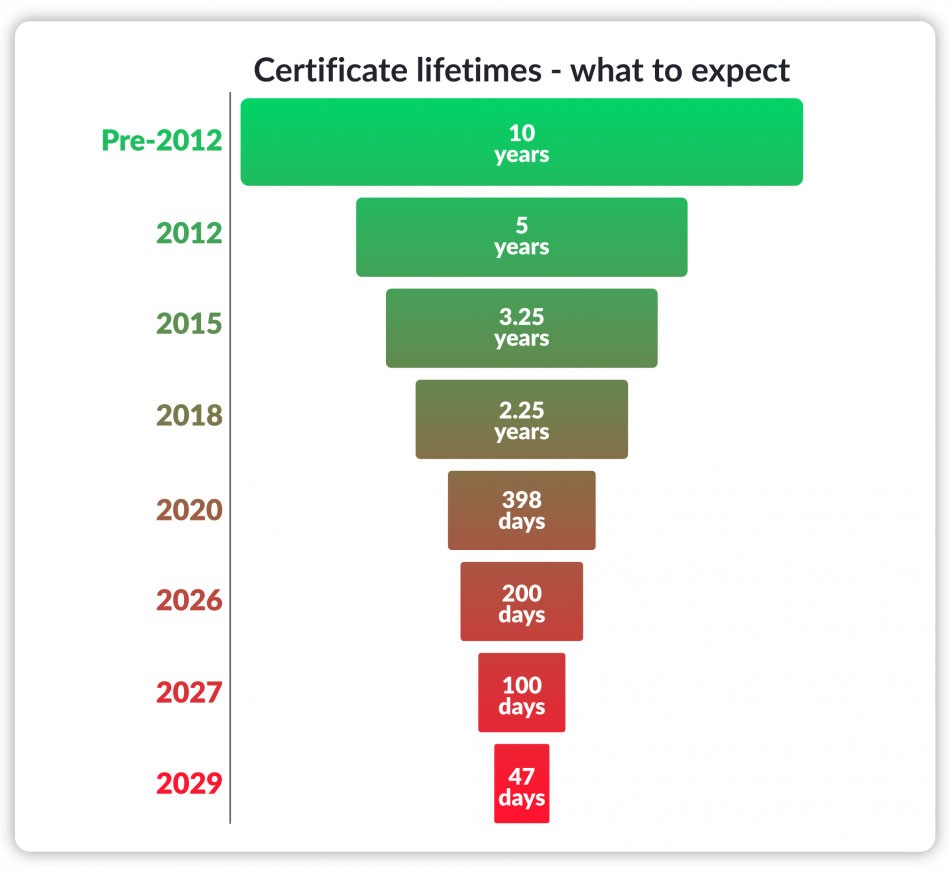
This change marks the first of three phases of shortening digital certificate lifespans:
- On March 15, 2027, validity periods will be halved to a maximum of 100 days (which means CAs will issue certificates typically with 99-day [or shorter] lifespans).
- On March 15, 2029, certificate lifespans will be capped at 47 days for max validity (read: 46-day [or shorter] certificates).
The Issue: What Does This Lifespan Reduction Mean for You?
This shift to 199-day certificates means that every publicly trusted SSL/TLS certificate you own or manage will have to be reissued twice as often. Putting it another way, that 15-or-so-minute task of reissuing and installing each SSL/TLS certificate within your company’s control is going to be doubled.
While this isn’t too bad for someone with just a handful of certificates, that time quickly adds up when you have 10, 20, or more.
For a quick illustration, let’s split the difference and imagine you have 15 SSL/TLS certificates to manage when the next lifespan reduction phases kick in:
- 200-day validity (2026) = 30 certificate reissuances per year
- 100-day validity (2027) = 60 certificate reissuances per year
- 47-day validity (2029) = 120 certificate reissuances per year
This means that starting in 2029, you’ll spend a minimum of 30 hours every year just reissuing and reinstalling certificates.
The Solution: Now’s the Time to Move to SSL Certificate Automation
Sectigo’s ACME Certificate-as-a-Service (CaaS) (coming soon) is the autopilot of certificate management. With ACME-based automation, you can set up your certificate once and CaaS will take it from there, handling it as a fully automated SSL certificate. It simplifies the certificate lifecycle and frees up time that would otherwise be spent on important but repetitive busywork.
Will it scale with your business and the decreasing validity periods? Absolutely — you pay per domain and enjoy unlimited certificates. And the best part is that it works with virtually all major ACME clients — acme.sh, certbot, cert-manager, Posh-ACME, and win-acme.
No more tedious, monotonous certificate management — just an opportunity to regain time that you can better spend elsewhere doing (ideally) other critical, non-repetitive tasks.
Note: Keep an eye out for these fully automated SSL/TLS certificates, which will roll out over the next couple of weeks.
Why Is the Industry Moving to Shorter Validity Periods?
About a decade ago, one word shook the PKI industry to its core: Heartbleed. This OpenSSL vulnerability went unnoticed for two years. Attackers exploited this security flaw to connect to a server and export 64KB of memory data at a time. What kind of data? Whatever they could get their hands on, including SSL/TLS private keys.
Cybersecurity expert Bruce Schneier described this vulnerability as being utterly catastrophic: “On the scale of 1 to 10, this is an 11.”
Consider the situation:
- Cybercriminals exploiting this security flaw used these cryptographic secrets to impersonate services and decrypt sensitive data transmissions.
- They were able to engage in these activities, unabated, anytime during the two-or-so years the bug was in the wild.
- The only way to mitigate the issue was to
- patch the bug,
- issue a new SSL/TLS certificate for your website (including the generation of a new public-private key pair), and
- update virtually every password in your environment (on the off-chance that they could have been compromised).
As a result, the journey toward shorter validity periods continues over the next several years.
Final Takeaway: Automate SSL and Reclaim Your Workweek
The discovery of Heartbleed was the impetus for an ongoing debate among industry leaders about the need for shorter certificate validity. Since then, we’ve seen the lifespans of publicly trusted SSL/TLS certificates reduced from five years to three years to one year (i.e., the current 398-day requirement).
We’re about to see the next set of phases roll out over the next three years, which will ultimately lower the maximum validity period to 47 days. Now’s the time to put manual SSL certificate management in your review mirror with automation. This will free you up from the tedious, ever-increasing tasks associated with domain validations, certificate reissuances, and deployments.





















2018 Top 100 Ecommerce Retailers Benchmark Study
in Web Security5 Ridiculous (But Real) Reasons IoT Security is Critical
in IoTComodo CA is now Sectigo: FAQs
in SectigoStore8 Crucial Tips To Secure Your WordPress Website
in WordPress SecurityWhat is Always on SSL (AOSSL) and Why Do All Websites Need It?
in Encryption Web SecurityHow to Install SSL Certificates on WordPress: The Ultimate Migration Guide
in Encryption Web Security WordPress SecurityThe 7 Biggest Data Breaches of All Time
in Web SecurityHashing vs Encryption — The Big Players of the Cyber Security World
in EncryptionHow to Tell If a Website is Legit in 10 Easy Steps
in Web SecurityWhat Is OWASP? What Are the OWASP Top 10 Vulnerabilities?
in Web Security