All posts in
Web Security
$900 million and counting — that’s the price the UnitedHealth Group is paying for a data breach and ransomware attack caused by weak authentication practices. PKI certificate-based authentication isn’t new,…
78% of GitHub’s developer survey respondents currently use (or plan to use) generative AI (GenAI) within two years. Explore OWASP’s GenAI Security Incident guide, which shares insights into how small-…
Learn from the past to prepare for the future with these 5 infamous cyber attacks (and their disastrous consequences) that could have been prevented with code integrity check. Operational downtime,…
By 2029, SSL/TLS certificates will be valid for a maximum of 1.5 months. Here’s what to know about the certificate validity period reduction that will begin rolling out in March…
More than half of the 29,065 vulnerabilities reported in 2023 had critical or high severity scores. Strengthen your defenses by running a website security check to uncover and fix weaknesses…
TLS is a secure protocol that protects sensitive information exchanges like passwords and credit card numbers against theft from cyber attacks (which are up 8% year-over-year for organizations). Here’s what…
Whether you’re a small business running your website or a website user, it’s imperative you know how to check if you’re using a secure connection. Here’s what you can look…
TLS handshake error can be annoying for users and site admins alike, but fixing it is easy and quick with these 8 fixes… When you try to open a website,…
In 2014, Mozilla moved away from using certificate revocation lists (CRLs) to check the validity of TLS certificates with the release of Firefox 28.0. So, do CRLs still matter? Yes,…
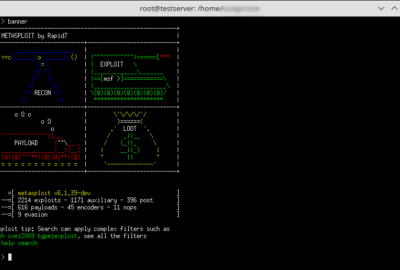
Metasploit Framework is an open-source platform that’s useful for detecting vulnerabilities and creating tools that enhance an organization’s network security. Let’s look at an overview of the Metasploit Framework and…





















2018 Top 100 Ecommerce Retailers Benchmark Study
in Web Security5 Ridiculous (But Real) Reasons IoT Security is Critical
in IoTComodo CA is now Sectigo: FAQs
in SectigoStore8 Crucial Tips To Secure Your WordPress Website
in WordPress SecurityWhat is Always on SSL (AOSSL) and Why Do All Websites Need It?
in Encryption Web SecurityHow to Install SSL Certificates on WordPress: The Ultimate Migration Guide
in Encryption Web Security WordPress SecurityThe 7 Biggest Data Breaches of All Time
in Web SecurityHashing vs Encryption — The Big Players of the Cyber Security World
in EncryptionHow to Tell If a Website is Legit in 10 Easy Steps
in Web SecurityWhat Is OWASP? What Are the OWASP Top 10 Vulnerabilities?
in Web Security