Apple Zero Click Attack: Can FORCEDENTRY Affect My iPhone?
Zero click attacks are not new, but the concept spread like wildfire after Pegasus spyware hit the headlines. FORCEDENTRY is the latest way for Pegasus to infect iPhones – so here’s everything you need to know about this Apple zero-click vulnerability
News about Pegasus spyware has shaken the world. Apple users in countries around the globe have growing concerns about whether their personal information is being leaked and aren’t sure what they can about it. Many of us know to be careful when opening attachments or links. But although being vigilant will help you avoid getting hacked, generally speaking, there’s a type of attack that can invade your device even if you don’t click anything. It’s called an Apple zero click attack.
In this article, we’ll examine the zero-click iOS vulnerability that allows Pegasus spyware to invade iOS devices and provide the latest updates about the situation.
The Bad News: An Apple Zero Click Attack Targeted iOS Devices
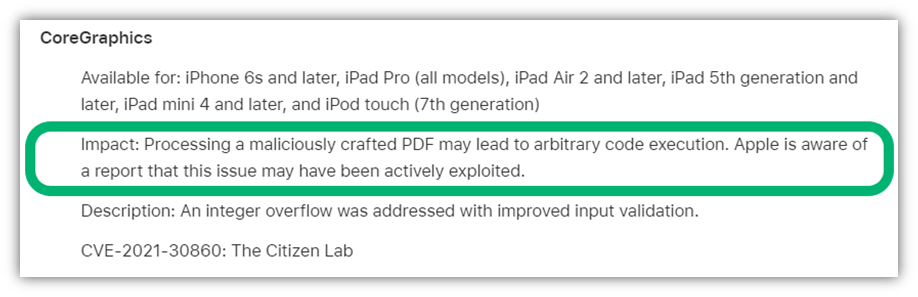
On Sept. 13, 2021, researchers at Citizen Lab published a report about a zero click exploit affecting Apple devices they named FORCEDENTRY. FORCEDENTRY’s malicious code was spread through the iMessages app and exploited a vulnerability in iOS’s image rendering library (CoreGraphics). This zero-click iOS exploit was used to deliver the infamous Pegasus spyware, which was created by the NSO group (a state-sponsored surveillance company in Israel).
While inspecting the phone of a Saudi activist, Citizen Lab’s scientists discovered that Pegasus spyware was delivered through a zero-click exploit and was being used for espionage. The researchers found 27 files with .gif extensions in Library/SMS/Attachments of the infected device, which were actually Adobe PSD and PDF files carrying the Pegasus payload.
FORCEDENTRY doesn’t require the victim to open the link they receive in iMessages for their device to become infected. But what makes things worse is another bug that kicks into effect called CASCADEFAIL. This vulnerability enables bad guys to delete critical entries from usage and process logs. In the case of FORCEDENTRY, this bug allowed the NSO group to delete the evidence from the phone’s DataUsage.sqlite file.
Yup, there’s a lot of bad news to sort through here. However, there’s also a silver lining: Pegasus isn’t a type of self-replicating malware. In other words, it stays on the targeted victim’s device and doesn’t get transferred to other people’s devices when the victim transfers any other data or messages to them from the infected devices.
The Good News: Apple Issued a Fix for the FORCEDENTRY Exploit
According to The Citizen Lab’s report, Apple has fixed this vulnerability and published a patch for iOS 14.8 and iPadOS 14.8 on Sept. 13, 2021. They named Apple’s zero-click vulnerability CVE-2021-30860 and asked everyone to update their software.
So, if you haven’t applied this update yet on your devices, you should do it now. This will fix the vulnerability that allows the FORCEDENTRY exploit to work in the first place.
More About Pegasus Spyware on iOS Devices
FORCEDENTRY has been active since February 2021, although the patch that fixes the exploit was issued by Apple in September 2021. It is linked to the previously discovered KISMET exploit, which was active between June 2020 and February 2021 and was used to spy on Bahraini activists. Apple fixed an underlying vulnerability in iMessage by introducing BlastDoor in iOS 14. According to The Citizen Lab’s report, NSO developed FORCEDENTRY to circumvent BlastDoor.
This is not the first time NSO group has exploited vulnerabilities in iOS to deliver Pegasus spyware. In fact, this spyware variant has been on the radar of The Citizen Lab’s security experts since 2016 when they published a report sharing that the NSO group was exploiting iPhone zero-day vulnerabilities to spy on a human right activist in the UAE.
Am I At Risk of a Zero Click Attack?
As far as Apple zero click Pegasus spyware is concerned, you probably don’t need to worry about it unless you don’t apply Apple’s update to your device, or you are a likely target:
- Political or human rights activists
- Union leaders and members
- Politicians and political party workers
- Journalists
- Lawyers
- Doctors
- Business leaders
- Diplomats
If you think you could be a target, install the latest iOS version and keep all your devices patched. If you notice any unusual activity or suspect that your information is being leaked, contact security experts or your local law enforcement department immediately. Most countries have cybersecurity/cyber forensic departments working together with local police to deal with internet-related crimes.
Although most of us don’t need to worry about Pegasus directly, it’s just one example of many zero click attacks. Hackers have been using zero click malware for many years to:
- Steal login credentials
- Monitor a victim’s actions
- Execute ransomware attacks
- Blackmail victims
- Steal research, trade secrets, and other sensitive data
So, yes, you could still be a victim of a zero click attack. To avoid these attacks and all the other types of malware out there, it is vital to follow the best internet hygiene practices.
Final Words on the FORCEDENTRY Apple Zero Click Exploit for iOS Devices
Although the NSO group claims that its software is helping nations to combat terrorism and crime, it is infamous for providing “despotism-as-a-service” to its clients for nation/state-sponsored espionage operations. The ongoing Pegasus debacle highlights the urgent need for global regulation of the multi-million dollar spyware business.
We can also infer from the situation that popular chat apps are highly vulnerable to zero click attacks. Previously, WhatsApp was used to deliver the Pegasus spyware. Companies developing such communication software must put rigorous effort into finding and fixing security vulnerabilities on an ongoing basis.




















2018 Top 100 Ecommerce Retailers Benchmark Study
in Web Security5 Ridiculous (But Real) Reasons IoT Security is Critical
in IoTComodo CA is now Sectigo: FAQs
in SectigoStore8 Crucial Tips To Secure Your WordPress Website
in WordPress SecurityWhat is Always on SSL (AOSSL) and Why Do All Websites Need It?
in Encryption Web SecurityHow to Install SSL Certificates on WordPress: The Ultimate Migration Guide
in Encryption Web Security WordPress SecurityThe 7 Biggest Data Breaches of All Time
in Web SecurityHashing vs Encryption — The Big Players of the Cyber Security World
in EncryptionHow to Tell If a Website is Legit in 10 Easy Steps
in Web SecurityWhat Is OWASP? What Are the OWASP Top 10 Vulnerabilities?
in Web Security