All posts in
Cyber Security
Identity Defined Security Alliance (IDSA) reports that nearly 85% of identity stakeholders were directly impacted by identity-related security incidents in 2023. Protect your data and systems by learning eight passwordless…
61% of small businesses victims of a cyberattack in 2023 lost over $10,000. Learn how to harden your digital defenses with these five NIST CSF 2.0 key points According to…
98% of small businesses were victims of at least one cyber attack in 2023. Help your company prepare for the worst with this free small business cyber security plan template…
SpyCloud recovered 721.5 million stolen credentials from the darknet in 2022. Don’t be the next victim. Go passwordless! Protect one of attackers’ favorite network entry points. Discover how to log…
Perfect forward secrecy in TLS 1.3 is what helps to prevent the encrypted session data you’ve sent or received from being decrypted should the receiving server’s private key become compromised…
Set your watch — we’ll cover all the PKI basics you didn’t know you didn’t know in less time than it takes to make a good cup of coffee Have…
Whether you’re a small business running your website or a website user, it’s imperative you know how to check if you’re using a secure connection. Here’s what you can look…
TLS handshake error can be annoying for users and site admins alike, but fixing it is easy and quick with these 8 fixes… When you try to open a website,…
A security honeypot is a great tool for mature cybersecurity researchers and defenders. This article explores what it is and how to create a honeypot that may help you learn…
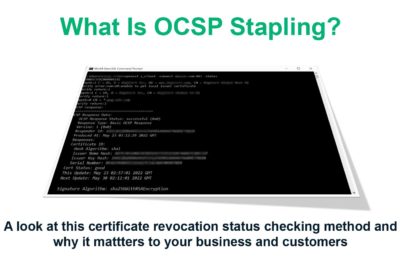
OCSP stapling makes verifying the revocation status of an SSL/TLS certificate faster and easier for a client than ever before. It’s an improvement on the current industry standard, OCSP. But…





















2018 Top 100 Ecommerce Retailers Benchmark Study
in Web Security5 Ridiculous (But Real) Reasons IoT Security is Critical
in IoTComodo CA is now Sectigo: FAQs
in SectigoStore8 Crucial Tips To Secure Your WordPress Website
in WordPress SecurityWhat is Always on SSL (AOSSL) and Why Do All Websites Need It?
in Encryption Web SecurityHow to Install SSL Certificates on WordPress: The Ultimate Migration Guide
in Encryption Web Security WordPress SecurityThe 7 Biggest Data Breaches of All Time
in Web SecurityHashing vs Encryption — The Big Players of the Cyber Security World
in EncryptionHow to Tell If a Website is Legit in 10 Easy Steps
in Web SecurityWhat Is OWASP? What Are the OWASP Top 10 Vulnerabilities?
in Web Security