What Android Ransomware Is & How to Protect Yourself from It
If you own an Android phone, you must be aware of a rising cyber threat called Android ransomware and how to deal with it.
Hackers are targeting Android smartphone users with new and inventive forms of Android ransomware. Last year, we saw the emergence of Android/Filecoder.C, and this year, it’s AndroidOS/MalLocker.B.
Android is the global leader in the mobile operating system, holding 85% of the market share and having more than 2.5 billion active users. This gigantic pool of potential targets is attractive to cybercriminals. So, if you’re an Android user and concerned about the security of your data and device, you’ve come to the right place. In this article, we’ll cover:
- What is Android ransomware?
- How does it damage your mobile?
- What to do if your phone gets affected?
- How can you prevent it?
So, without any further delay, let’s explore the topic of ransomware for Android devices.
What Is Android Ransomware?
Android ransomware is a variant of malicious software (malware) that targets mobile devices running on Android operating systems.
Android ransomware attacks are like kidnapping. Hackers install malware variants (viruses, trojan horses, rootkits, worms) inside victims’ Android phones. It steals or encrypts data on users’ devices, or blocks the users from accessing their phones by freezing the device screens. Then attackers blackmail the victims for extortion money in exchange for access to their devices or data.
A mobile ransomware attack may involve any or all of the following tactics:
- Encrypting data and demanding extortion money in exchange for access to the affected data.
- Locking the phone or the screen in a way that users can’t use any of the functionalities until they pay the ransom.
- Stealing personal information or sensitive media files, and threatening to disclose it in the public domain if they don’t receive payment.
Android ransomware generally stays dormant on infected devices, altering the coding in the background silently, and setting a trigger for users to activate. A trigger could be an action such as a user trying to make a call or opens a particular website or app. As soon as the user activates the trigger, the ransomware starts doing its job (i.e., encrypting the data or locking the device). Then, the device’s screen shows the ransom demanding
Examples of Android Ransomware
Let’s take a look at a few examples of Android ransomware messages:
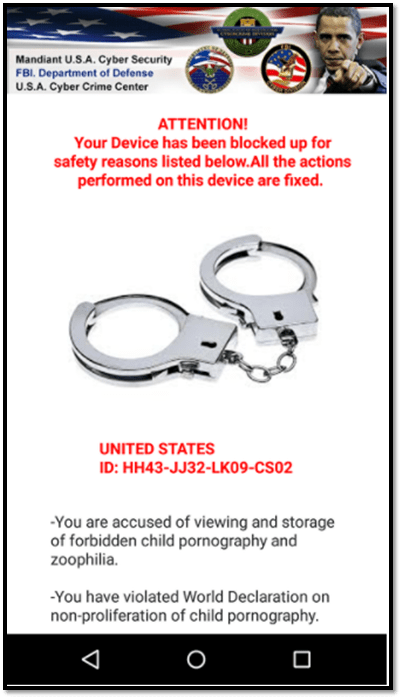
In the image above, a Koler.a ransomware note aims to generate panic in victims to manipulate them into paying a ransom.
In the same way, the Android ransomware variant SimpLocker masquerades as the NSA or FBI. This type of ransomware locks the phone and encrypts the files, demanding that users pay a fine to regain access to their device.

Categories of Android Ransomware
ESET identifies two main categories of Android ransomware:
1. Crypto ransomware: This group of ransomware encrypts important data, documents, files, media content, etc. The threat actors use cryptographic keys to lock and unlock the data, and the hacker demands a ransom in exchange for a decryption key. (The hacker may or may not give you the decryption key, and even if they do, there’s no promise that it will work.)
2. Locking ransomware: The hackers control the entire user interface (UI) and lock the phone. The ransomware notice stays on top of all other windows. So, no matter which buttons victims press, they can’t delete the popups or access anything on their devices until they pay the ransom or have the right technological tools to get rid of it.
Android ransomware like MalLocker.B and Koler.a are classic examples of locker ransomware. They lock the phone screen and display ransom notes impersonating law enforcement. These messages claim that users have committed an online crime and must pay a penalty to regain access to their phones.
How Does Android Malware Get Inside Your Phone?
Okay, you know what Android ransomware is and what it does. Now, it’s time for the million-dollar question: how does the ransomware infect your smartphone in the first place?
Android malware is commonly spread via:
- Third-party websites,
- Phishing email attachments,
- Discussion forums (where hackers participate in group discussions and post malicious links that appear to have related information),
- Social media platforms (through infected games, links, surveys, or malvertisements),
- Infected apps that are commonly distributed through third-party app stores, and
- SMS phishing (smishing) schemes.
Cybercriminals can also distribute Android malware using trojans, malicious links, and various social engineering tricks. They disguise malware as well-known applications, cracked versions of software, games, media players, or antivirus software. When users click on such a link, the malware gets installed on their phones and take control of the back-end coding.
How Android Ransomware Malware Works
Android ransomware is an evolving threat. According to Microsoft’s 365 Defender Research Team, Android malware historically would exploit the platform’s SYSTEM_ALERT_WINDOW functionality. This feature on Android phones would showcase notifications requiring users’ immediate attention that couldn’t be dismissed. And like many other good things in life, hackers twisted this functionality to suit their evil deeds to display ransom notes.
To combat this, Google introduced a “kill switch” in Android OS versions 8.0 and later, which allows users to turn off the alert window. Earlier, it just needed a single click to approve the apps/software permission to access SYSTEM_ALERT_WINDOW functionality, which users tend to overlook. But now, users have to go through many screens to grant such permission.
The latest evolution in Android ransomware, as identified by Microsoft’s 365 Defender Research Team, involves the following process:
- Building Notifications: Once Android ransomware installs on a device, it starts building a notification carrying the ransom notice. It uses the setCategory(“call”) function to indicate that the notification is highly important and needs special privileges.
- Hijacking the Screen: The notification is stored in the graphical user interface (GUI), and when the user clicks on the notification or any pre-decided trigger, API pushes the ransomware notification window using setFullScreenIntent() functionality.
- Blocking the users to access anything else: As soon as the ransom snippet pops up on the screen, it blocks the onUserLeaveHint() functionality of the Android device. That means, even if users hit the back button to close the snippet, they will be barred from doing so. If they try to use any other phone functionality, the main screen won’t show it, and the top screen will remain intact with a ransom notice.
How to Deal with Android Ransomware
What to do if your phone gets infected with Android ransomware? FBI doesn’t advocate paying a ransom, because there’s no guarantee that cybercriminals will give you back access to your data or device. Some ransomware variants are made so that once the data is encrypted, you can’t decrypt it even with the decryption key. Plus, if you pay a ransom, the concern is that it’ll further motivate hackers to continue their illicit activities in the future. Hence, instead, try the following tips.
1. Quarantine the Infected Device
As soon as you think your phone is infected with Android ransomware, disconnect it from all networks, including Wi-Fi. The hackers use Wi-Fi to spread malware to other connected devices. If the phone is using cellular data, remove the SIM card. Hackers generally need the internet to control the malware in your device. So, quarantining the phone from the internet would help to cease the infection from spreading further.
If your phone is connected to other devices like a smartwatch, Bluetooth speakers, or a printer, then disconnect the phone from them, too. You might be tempted to plug your phone into the PC to take the backup and access some functionalities — DON’T do that! The ransomware will spread to your PC and infect it, too.
2. Use Online Decryption Tools
Once the phone is quarantined, use tools like CRYPTO SHERIFF, ID Ransom, or Bitdefender to try to determine which type of ransomware has infected your Android device.
After figuring out the type of ransomware, you might be able to use these decryption resources to try to unlock your device or data:
3. Open Your Phone in Safe Mode
If you haven’t taken a backup of your data and want to save the data, you can try to reboot the phone and open it in safe mode. This option will make all the third-party apps that you have installed.
- Press and hold the power button. You will see options like Power off, Restart, Emergency, etc. (depends upon the phone manufacturer)
- From those options, hold the Power off icon (on the screen) for a longer period.
- You will see a screen that says Reboot to safe mode. Tap OK and wait for the device to reboot.
From here, create a backup of your data and reset the phone (next step). However, you should know that it’s a risky practice to backup data from an infected phone. It might spread the virus in the other connected device as well. But if you must, at least make sure all the backup is scanned with strong security software (which we’ll cover shortly) at the time of transferring into a new device.
Note: If the malware has spread from the original app to the other parts of your device, this option might not work. If you’re still seeing the ransom note on the screen, resetting the phone might be the only option you have left.
4. Reset to the Device’s Factory Settings
If your phone screen is showing the ransom note and you are not able to close the window or access anything on the phone, then the only option is to reset the device.
This option will delete all your data (including infected apps and the malware) and bring the phone in the same condition as it was when you bought it. It is known as factory reset.
Select the phone manufacturer to follow the reset steps.
5. Report the Cybercrime to Law Enforcement
If the hacker is blackmailing you to release your sensitive data to the public or misuse them, it is a serious extortion case, and you should file a report in your local police department. Most countries have a cybercrime department working with police to handle these types of cases.
How to Prevent Android Ransomware
These are some easy steps smartphone users can take to protect themselves from Android ransomware and other cyber threats.
1. Use a Robust Security Software Tool
Security software not only detects and removes malware but also can warn you when you visit an infected site or download a malicious app. Auto-install variants of malware may download or install onto your mobile without you noticing. A good security program scans and notifies you every time something downloads to your device.
We have listed some freemium security software below.
2. Be Careful While Clicking on Unknown Links and Downloading Apps
If you see any links on the comments on discussion forums, on unknown sites, or embedded in emails (especially when the email is coming from an unknown sender), avoid clicking on them.
If anyone is offering a free version of popular commercial products such as software, songs, PDF files, games, or slideshows, be very cautious and don’t download if it is avoidable. If you must, at least scan them with robust anti-malware software before downloading.
3. Read Reviews Before Downloading Third-Party Apps
When you are downloading a new, unknown or unpopular app, read the reviews first. If you see low ranking/stars and if any user is complaining about a security issue or a general infection sign. Messages like the following could indicate signs of an infected or compromised app:
- The app made my phone too slow.
- It downloaded some other app/software onto my phone.
- The appt redirects me to some other website.
- It shows inappropriate popups.
- My phone started to show advertisement windows after installing this app.
If you see apps with reviews like these, you should not install them. You can also conduct a separate search for the developer (company or person) to read the reviews.
4. Always Keep Backups
Regularly create backups of your data — pictures, videos, documents, and anything else worth storing. The best place to store a backup is a secure third-party cloud platform. If you want additional backups, you can store them on USB drives, portable hard drives, or your PC.
If Android ransomware has encrypted your data on your device, you can easily recover it from your backups.
5. Keep an Eye on Apps and Their Permissions
You should give administrative privileges to only those apps which you 100% trust and belong to reputable companies and developers. Follow the below path to check which have administrative privileges on your phone:
Go to Settings > Security > Device Administrators. (Note: this path might change based on the phone’s specific manufacture.)
Uncheck all other unknown, unnecessary apps from this list. If you see any apps that you haven’t installed, or that didn’t come pre-installed on your device, immediately delete them.
6. Don’t Root Your Android Phone
Rooting the phone means changing the phone’s default settings by gaining greater administrative privileges. It’s kind of like the Android equivalent of jailbreaking an iPhone. People root their phones to tweak their appearance, access blocked apps, unlock the devices (to change the default service provider), etc. But rooting is a highly dangerous practice, and it removes a lot of the default safety measures Google has in place to protect Android users.
Rooting will weaken your phone security mechanisms, and hackers can easily install all types of malware, including Android malware.
Final Thoughts on Android Ransomware
Some people may want to “play it safe” by paying the ransom to save try to save their expensive phones or regain access to their data. But as you’ve learned, even that move isn’t without risks. After all, there’s no guarantee that even after receiving money, the hacker won’t demand additional ransom or give you back access to the encrypted data. Nor does it promise that they won’t target you again in the future.
Instead, you should familiarize yourself with cybersecurity best practices that help you to avoid becoming a victim in the first place. Otherwise, you can familiarize yourself with the techniques, tools, and software you can use to deal with this Android ransomware and regain access to your phone without paying a ransom.














 (49 votes, average: 4.92 out of 5)
(49 votes, average: 4.92 out of 5)






2018 Top 100 Ecommerce Retailers Benchmark Study
in Web Security5 Ridiculous (But Real) Reasons IoT Security is Critical
in IoTComodo CA is now Sectigo: FAQs
in SectigoStore8 Crucial Tips To Secure Your WordPress Website
in WordPress SecurityWhat is Always on SSL (AOSSL) and Why Do All Websites Need It?
in Encryption Web SecurityHow to Install SSL Certificates on WordPress: The Ultimate Migration Guide
in Encryption Web Security WordPress SecurityThe 7 Biggest Data Breaches of All Time
in Web SecurityHashing vs Encryption — The Big Players of the Cyber Security World
in EncryptionHow to Tell If a Website is Legit in 10 Easy Steps
in Web SecurityWhat Is OWASP? What Are the OWASP Top 10 Vulnerabilities?
in Web Security