What Is a Digital Signature and How Does the Digital Signature Process Work?
What is a digital signature? It’s probably not what you think it is… in fact, you’re using several right now…
Although it’s easy to confuse the two, a digital signature isn’t the same thing as an electronic signature. Although both terms include the word “signature,” and they both relate to identity, they’re actually two different processes. A digital signature is a type of electronic signature in the broad sense, but it serves a different function and end goal.
A digital signature is also different than a digital certificate (although the two work in conjunction). Not sure what we mean? You’ll see shortly. In this article, we’ll break down what a digital signature is and how it works. We’ll also dive into the nitty-gritty things to know about the digital signature process as a whole.
What Is a Digital Signature in Cryptography?
In a nutshell, a digital signature (also known as an advanced electronic signature or qualified electronic signature, in some cases) is an integral component of public key infrastructure (PKI) that allows users to look at something (an email, document, software application, etc.) and know who it came from. Basically, it’s a way for you to authenticate yourself to another party and show that your item in question is legitimate and unaltered. For example, here’s how a digital signature looks in a signed email:
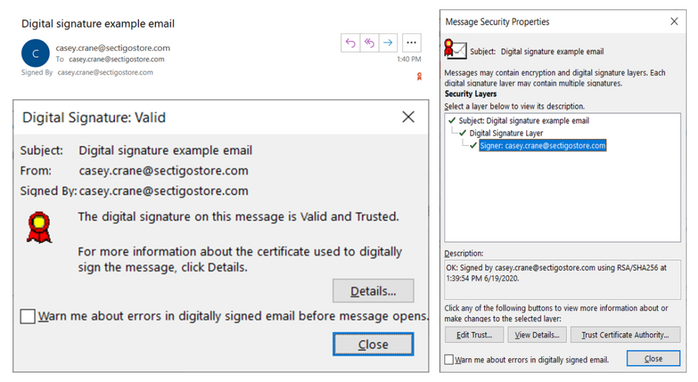
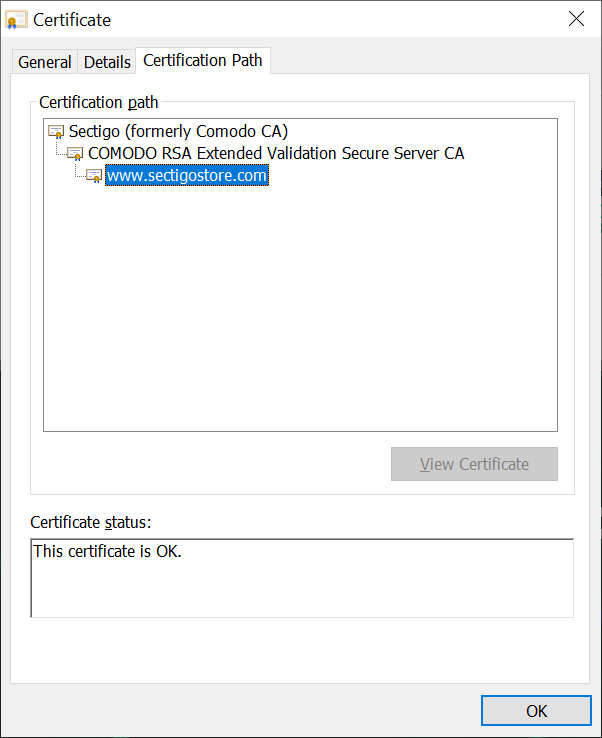
Another example of a digital signature can be found in SSL/TLS certificates in the form of the certification path. For example, the SSL/TLS certificate on SectigoStore.com is signed by the intermediate certificate using a digital signature, which is signed by the root certificate, so you can know for sure that this website was verified by Sectigo:
Digital signatures work hand-in-hand with hash functions, or what are known more simply as hashes. Ever heard of SHA-2 and SHA-256? Yeah, those are two of the most common examples of hashing algorithms. (Don’t worry, we’ll talk more about hashing a little later to provide additional clarity.)
Digital Signatures Offer Assurance and Authenticity
… Hmm, that didn’t really help much, did it? Okay, let’s try this another way. There are three primary uses for digital signatures:
- Authentication — You’re using a trusted third party such as a certificate authority (CA) to validate that you are the person you claim to be.
- Non-repudiation — What this means is that no one can deny (repudiate) that it was, in fact, you who sent a message or published a piece of software.
- Message integrity — This shows the recipient, email client, OS or server that the data hasn’t been tampered with in any way since it was signed. (Note: A digital signature doesn’t actually stop someone from tampering with signed data — it just indicates whether someone has or not so you can make a decision about whether to trust its integrity.)
Okay, it probably sounds like something you’d never end up using in daily activities, right? Wrong — and here’s why.
How a Digital Signature Can Be Used in Real World Applications
Wondering what a digital signature is in terms of how your organization can use it in the real world? You may be surprised to know that many companies and organizations are already using digital signatures. In fact, if you’ve ever downloaded an app on your computer that displayed a pop-up with the name of the developer or manufacturer who created it, that means that you’ve seen the results of a digital signature application.
You can use digital signatures in a variety of applications:
- Email sender authentication
- Document and certificate authentication
- Software authentication
Some of the most common types of PKI digital certificates that use digital signatures include:
- Email signing certificates (AKA personal authentication certificates, S/MIME certificates, client certificates, etc.)
- Code signing certificates
- SSL/TLS certificates
What Is the Digital Signature Process?
Now that we have a better understanding of what a digital signature is and what it does from a high-level perspective, it’s time to roll up our sleeves and really dig in to how it works on a more technical level.
The digital signature process is based on asymmetric cryptography because it involves the use of a set of mathematically related public and private keys.
![]() Hashing (and Hash Values)
Hashing (and Hash Values)
In a nutshell, hashing is a simple way of generating a code that uniquely identifies a file. If the file changes, the hash value changes, too. This means that a hash, for all intents and purposes, is a one-way function that can be applied to a piece of data of any length to produce a unique string of text (what’s known as a hash value, digest, or fingerprint) of a fixed length.
This hash digest is encrypted using the message creator’s private key (and the creator’s public key decrypts it on the end user’s side). The purpose of a hash is to serve as a checksum that proves that the message, code, or whatever it has that’s been hashed hasn’t been altered. (This differs from encryption because encryption is intended to be a two-way process.)
Basically, it takes your message and applies a hash function (such as SHA-256) to it that converts it into a hash value like this:
HELLO = ch857er1iu23rbhfiu23rhb2c2b4l8m4n
(Okay, technically, it’s theoretically possible for someone to reverse a hash using brute force. But the amount of time and computational resources that would be required really makes trying to do so pretty pointless…)
It’s important to note that every hash value is unique. If there are two different files that somehow manage to product the same hash value, this results in something called collision. Much like a vehicle collision, a hash collision is also bad. Basically, it means that the hash algorithm is useless and won’t protect your file or message.
Anyhow, to help you better understand what a hash is, let’s think of it in terms of digitally signing an email. You can use an email signing certificate to digitally sign your email. This helps you prove to your recipient that it was you who sent the message and that it hasn’t been tampered with since you pushed “send.” (This gives you the authentication and message integrity assurance that we referred to earlier.)
A Look at the Digital Signature Process (for Email) in Action
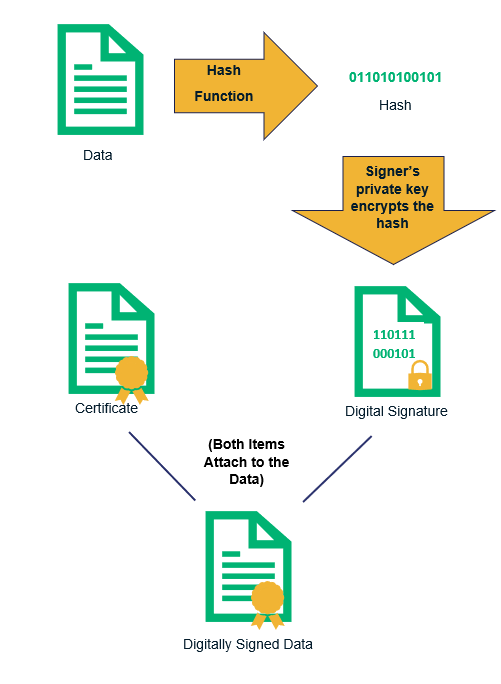
Okay, so let’s take a look at how the digital signature process actually works in terms of sending an email:
- Purchase an email signing certificate. You can get one from a reputable digital certificate provider (you know, like Sectigo). You have to go through the validation process and all that, but once you have the digital certificate, you’re able to move on to step two.
- Install your email signing certificate in your email client. We won’t tell you how to do that here because the process differs from one email client to the next. (Here’s the directions for how you can install and use one of these certificates in Outlook.) But don’t worry, it’s a one-time process to install it anyhow. When properly configured, your digital signature can be set to auto-apply to all of your outgoing messages after that.
- You create a message that you intend to send. This includes writing any text and attaching any other media.
- You (automatically) apply the hash algorithm to your message. Hashing the message (and any attachments) adds greater security. Because it’s automatic, you don’t need to actually do anything when digital signing is enabled. (Your email client does it for you.)
- Using your email signing certificate, you apply your digital signature to the message. This maps your email message to a fixed length output. It uses your public key to digitally sign it. Again, this happens automatically — your email client does the work.
- The hashed message and hashed signature are then encrypted. This is the icing on the cake if you have email encryption enabled. This process is what allows you to send the data across potentially insecure transmission channels. So, when your message leaves your email client and travels from one email server to another, even if someone intercepts the message, they can’t read it. (Encrypting data at rest requires the recipient to also have an email signing certificate as well, though, and you’d have to have the recipient’s public key, but that’s a process for another article).
- You transmit the digitally signed and encrypted message. This leaves your email client and transmits across the internet, going from your email server to theirs (and then on to their email client).
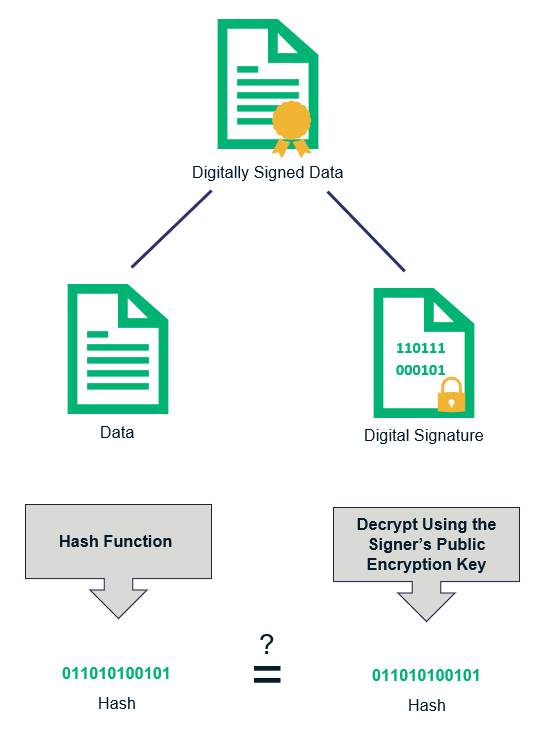
- Your recipient validates the digital signature using the same algorithm and your public key. Part of this process is recreating your hashed digest.
- Your recipient’s email client inspects the two unique hash values. The hash value that’s created is compared with the one attached in your message to ensure that they match. If they match, it means that the email is unaltered —all is hunky-dory and your recipient can go about their business. If they don’t, they’ll receive a warning message that indicates something’s wrong with your email, which casts you (and your organization) in a very bad light. Not so hunky-dory.
The Last Word on Digital Signatures
As you’ve learned, digital signatures are a great way to assert identity and to authenticate data and the people responsible for creating or sending it. They also work hand-in-hand to validate the integrity of the data in question by indicating whether it’s been tampered with (although it can’t stop the tampering event from happening in the first place).
Digital signatures in cryptography have a lot of different uses — they’re an essential part of information security for websites, documents, emails, and more. Fun fact: You use digital signatures every day, even if you’re not aware of them. Your browser uses multiple digital signatures to verify our website when you clicked to read on this article.














 (55 votes, average: 4.71 out of 5)
(55 votes, average: 4.71 out of 5)






2018 Top 100 Ecommerce Retailers Benchmark Study
in Web Security5 Ridiculous (But Real) Reasons IoT Security is Critical
in IoTComodo CA is now Sectigo: FAQs
in SectigoStore8 Crucial Tips To Secure Your WordPress Website
in WordPress SecurityWhat is Always on SSL (AOSSL) and Why Do All Websites Need It?
in Encryption Web SecurityHow to Install SSL Certificates on WordPress: The Ultimate Migration Guide
in Encryption Web Security WordPress SecurityThe 7 Biggest Data Breaches of All Time
in Web SecurityHashing vs Encryption — The Big Players of the Cyber Security World
in EncryptionHow to Tell If a Website is Legit in 10 Easy Steps
in Web SecurityWhat Is OWASP? What Are the OWASP Top 10 Vulnerabilities?
in Web Security