All posts in
Cyber Security
Cybersecurity Ventures predicts cybercrime damages will hit $6 trillion annually by 2021 — we’ll cover the best ways you can stop your organization from becoming the next statistic At one…
TLS 1.3 is used by 30% of connections on Chrome and 27% on Firefox, according to the IETF. Here’s what to know about TLS 1.3 and what this latest TLS…
Here are some of the key takeaways for companies and individuals from the DoD Cyber Awareness Challenge 2020 The Cyber Awareness Challenge, which is also known as the Army Cyber…
Here’s a non-techie look at how SSL and SSH are similar yet entirely different concepts “What’s the difference between SSH and SSL?” and “SSH vs SSL — which is better?”…
PCI DSS is a complicated subject, but it’s importance because noncompliance can cost you tens of thousands of dollars every month! Here’s a primer on how to adhere to PCI…
SecDevOps is an approach to integrated and secure product development — considering that Checkmarx reports that 92% of surveyed global organizations struggle with integrating security into their DevOps processes, it’s…
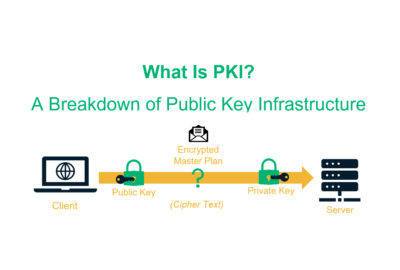
If you’ve wondered what public key infrastructure (PKI) is, you’ve come to the right place. It’s something that protects our money, privacy and so much more. The crazy part, most…
17 website, IT and cybersecurity professionals weigh in on how to make a website secure (and things you should avoid doing) with their expert tips If you’re not sure “how…
Doxxing is a cyber threat without boundaries — anyone can be a victim of doxxing regardless of their age, race, nationality, gender, or religion The internet is a double-edged sword:…
SSL_ERROR_RX_RECORD_TOO_LONG – Not sure what this error is or why you’re getting it? Here’s what to know about it and how to get rid of it If you’re wondering how to…














 (45 votes, average: 4.82 out of 5)
(45 votes, average: 4.82 out of 5)







2018 Top 100 Ecommerce Retailers Benchmark Study
in Web Security5 Ridiculous (But Real) Reasons IoT Security is Critical
in IoTComodo CA is now Sectigo: FAQs
in SectigoStore8 Crucial Tips To Secure Your WordPress Website
in WordPress SecurityWhat is Always on SSL (AOSSL) and Why Do All Websites Need It?
in Encryption Web SecurityHow to Install SSL Certificates on WordPress: The Ultimate Migration Guide
in Encryption Web Security WordPress SecurityThe 7 Biggest Data Breaches of All Time
in Web SecurityHashing vs Encryption — The Big Players of the Cyber Security World
in EncryptionHow to Tell If a Website is Legit in 10 Easy Steps
in Web SecurityWhat Is OWASP? What Are the OWASP Top 10 Vulnerabilities?
in Web Security