What Is PCI DSS? A Quick Guide to the 12 PCI DSS Requirements
PCI DSS is a complicated subject, but it’s importance because noncompliance can cost you tens of thousands of dollars every month! Here’s a primer on how to adhere to PCI DSS compliance requirements and to avoid fines and penalties
Did you know that only one in five organizations in the Americas maintain full PCI DSS compliance? Data from Verizon’s 2019 Payment Security Report indicates that only 36.7% of companies globally are fully compliant. This is why it’s important that you can answer the question, “what is PCI DSS?” and know how to apply it to ensure compliance.
When you are providing payment card details to a website while doing online shopping, how can you be sure that your sensitive data will be safe with the merchant? Just like most people, you trust that the merchant has followed some specific security procedures to protect users’ financial information. And you’re right. The merchants, vendors, and organization that that accept, transmit, process, or store payment card data need to adhere to the global guidelines and standards stipulated by PCI DSS.
If your organization handles payment card data, you must know what PCI DSS is and how it affects the security structure of your business. In this article, we’ll answer your questions surrounding the topic of what PCI DSS stands for, who regulates it, and “what are the main PCI DSS requirements?”
What Is PCI DSS?
Simply put, PCI DSS stands for the Payment Card Industry Data Security Standards. These 12 information security standards are designed to help businesses and organizations around the world securely handle payment cardholder data.
These requirements guide organizations to help them develop and implement policies, technologies, and processes surrounding payment card data. The standards define payment cards as:
“[…] any payment card/device that bears the logo of the founding members of PCI SSC, which are American Express, Discover Financial Services, JCB International, MasterCard Worldwide, or Visa, Inc.”
Who Must Be PCI DSS Compliant?
Not sure whether the PCI DSS compliance requirements apply to you? Well, if you handle any kind of credit or debit card information, then you do! Although these requirements are not actually considered laws or regulations in the legal sense, these standards affect any organizations that are associated with the use of payment cards in some way. This list of applicable organizations includes:
- Financial institutions, banks, and merchant banks
- Brick-and-mortar and ecommerce merchants,
- Service providers,
- Point-of-sale vendors.
What Do These Standards Cover?
In addition to knowing who these standards apply to, it’s also essential to know what they cover. All system components that are located within or connected to the cardholder data environment are covered under PCI DSS.
It includes:
- People, processes, and technology that handle cardholder data or sensitive authentication data.
- Network devices i.e. wired and wireless, servers, computing devices, and applications.
- Virtualization components, i.e., virtual machines, virtual switches/routers, virtual appliances, virtual applications/desktops, and hypervisors, etc. that accepts, transmits, and store cardholder data.
With all of these things in mind, now it’s time to get into the nitty-gritty of PCI DSS so you can understand its compliance requirements.
What Are the Main Components of PCI DSS?
These data security stands contain a set of security rules and guidelines for all the businesses that accept, process, and store the customers’ payment card details. When the merchant implements the required guidelines, their business is considered to be PCI DSS compliant. All the major payment card brands have made it mandatory for the merchants to be PCI DSS compliant. The main purpose of PCI DSS compliance is to:
- Protect the end-users’ card data,
- Mitigate the risk of various financial and identity frauds, and
- Determine the merchant’s liabilities in an unfortunate event of a cyber-attack.
Creators and Administrators of PCI DSS
PCI DSS was created by the five major card companies, i.e., Visa, MasterCard, American Express, American Express, and JCB. The first draft (called PCI DSS version 1.0) was released in 2004. In 2006, these companies established the Payment Card Industry Security Standards Council (PCI SSC) for the administration and development of the PCI DSS.
Any private organization can register with the council and provide their suggestions to revise and further develop the PCI DSS. The latest updated version, PCI DSS 3.2.1, was released in 2018.
Legal Requirements and Enforcement of PCI DSS
In the United States, firms are not legally required to be compliant with PCI DSS by federal law. But they do refer to PCI DSS’s guidelines to check the security structure strength of the firms and to determine the firms’ liabilities in the events of cybercrime or data breach incidents. Three states — Nevada, Minnesota, and Washington — have incorporated the PCI DSS into state laws.
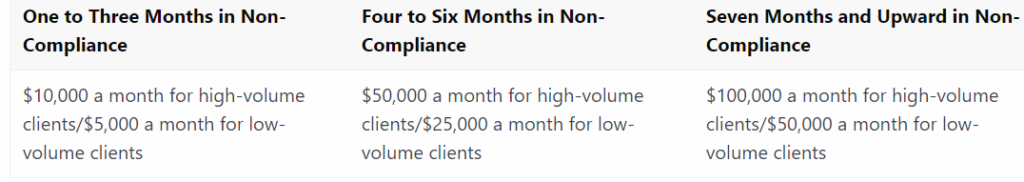
However, the card scheme has set fees and penalties if the merchants were not PCI DSS compliant at the time of data breach. These penalties can be as below.
It’s important to note, however, that compliance is not enforced by the PCI Security Standards Council. Instead, enforcement is the responsibility of the payment card companies themselves (VISA, Mastercard, etc.).
PCI Compliance Levels
Do you need to follow all the requirements stated in the PCI DSS? No! It has set the compliance levels based on the number of transactions a business encounters every year. So, if you’re a small business or a startup, you will need to follow only the basic set of rules as required in the compliance level set by your card issuer.
Level 1 – Businesses handling more than 6 million transactions annually must comply will all the regulations needed by this level.
Level 2 – Businesses having 1 to 6 million transactions annually falls under this category.
Level 3 – Businesses with annual transactions between 20,000 and 1 million.
Level 4 – Businesses having less than 20,000 transactions annually, i.e., startups and small businesses need to follow guidelines required at this level.
Audits and Assessments
It’s crucial to note that PCI compliance is a continuous, ongoing process that involves three critical steps:
- Assessment of cardholder data and assets, processes, remediation, and reporting.
- Remediation of vulnerabilities and elimination of data (if applicable).
- Reporting required information and documentation to the proper authorities (acquiring banks and card brands)
Any organization that’s subject to PCI DSS needs to hire an external Qualified Security Assessor (QSA) to perform the audit of their security posture and to certify whether the business is PCI DSS compliant. There is also a self-assessment questionnaire (SAQ), and only an Internal Security Assessor (ISA) can perform the self-assessment. An ISA is a company employee that has acquired the certification from the PCI SSC to perform the self-assessment for their firm. This SAQ must be submitted by the merchants to the banks every year to display the status of their PCI DSS compliance.
PCI DSS Structure
To really answer the question “what is PCI DSS?” you need to understand the structure of the standards. PCI DSS has six main control goals, 12 core requirements, and many other sub-requirements that a business must meet to be considered PCI DSS compliant. Each requirement is explained in three parts named requirement declaration, testing processes, and guidance.
The below table describes all 12 PCI DSS requirements, the objectives’ categories in which they belong, and a short description of each requirement:
| Control Objective | Core Requirement | Clarification |
| 1. Build and Maintain a Secure Network | 1. Use firewalls | Firewalls block all the incoming malicious requests and prevent unauthorized access to the data. |
| 2. Change the vendor-supplied default passwords and other security settings. | These passwords are weak, easily guessable, and sometimes publicly available, which weakens overall security. | |
| 2. Protect Cardholder Data | 3. Protect stored data using encryption, hashing, or masking. | Strong mathematical algorithms such as RSA, ECC, etc., scramble the stored data and make it incomprehensible. No one can read, interpret, steal, or modify such data. |
| 4. Encrypt transmission of cardholder data | A TLS/SSL certificate is required to secure the data in transit. | |
| 3. Maintain a Vulnerability Management Program | 5. Use an anti-virus or anti-malware software | The anti-virus tool constantly monitors, detects, and removes the viruses, internet worms, spyware, trojan horses, and other types of malware that can otherwise exploit the system. |
| 6. Develop and maintain secure systems and applications | Security patches and weak security infrastructure in the systems and applications make the overall security posture weaken. They must be sturdily built and frequently updated. | |
| 4. Implement Strong Access Control Measures | 7. Grant access cardholder data to only authorized personnel. | Only the employee who has “need-to-know” should have access to the customers’ payment card details. Restricts the unauthorized access to alleviate insider threats. |
| 8. Assign a unique ID to each employee | It is a crucial step to determine accountability and authorization. | |
| 9. Restrict access to the physical system that contains cardholders’ data. | Secure the physical systems where payment card details are stored to mitigate the risk of unauthorized data removal or theft. | |
| 5. Regularly Monitor and Test Networks | 10. Track and monitor who is accessing the cardholder’s data and other resources. | Deploying a change-monitoring system to track any authorized changes or suspicious employee activities to track whether they are accessing the confidential cardholder’s data without a “need to know.” |
| 11. Regularly check systems, software, processes to find out and fix vulnerabilities. | Vulnerability in the software and systems are used by cybercriminals to execute the cyber-crimes. Such security vulnerabilities must be constantly monitored and fixed on regular bases. | |
| 6. Maintain an Information Security Policy | 12. Have a security policy in the organization for all the employees | Develop the security policy and train the employees to make them understand the sensitivity of the data, various types of cyber risks, and best practices to mitigate those risks. |
To check out more details about these PCI DSS requirements, please visit this PCI compliance guide.
Wrapping Up
As a business owner, it’s both your legal and also moral responsibility to protect your customers’ any sensitive data (under laws and regulations like the CCPA, FIPS, GDPR, etc.). PCI DSS guidelines are an excellent resource to understand the various security vulnerabilities that leave cardholder data insecure, what damages such vulnerabilities can cause, and the actions you can take to mitigate the risks.
When a data breach or cyber-attack takes place, compliance with these guidelines will provide you a shield against the heavy legal penalty. It shows that you have taken bona fide measures to protect your customers’ data. On the other hand, the noncompliance with PCI DSS will not only attract hefty fines, but it will also spoil your relationships with the payment card companies and banks. Hence, always use underlying guidelines of the PCI DSS to develop a robust security posture.
We hope this article has sufficiently answered your questions about “what is PCI DSS?” and “what is PCI DSS compliance?”























 (51 votes, average: 4.76 out of 5)
(51 votes, average: 4.76 out of 5)






No comments