What Is Encryption and How Does It Work?
Explore why the tech industry is so fond of encryption and why it’s a founding pillar of data security!
You might not be aware of it, but you use encryption every day while surfing online. Even right now, when you are reading this article, the data between you and our server is constantly getting encrypted and decrypted in the background! but, what is encryption, and how does encryption work?
In this article, we’ll cover the meaning of encryption, what does encryption do, and its practical usage in the cybersecurity industry.
What Is Encryption?
Encryption means decoding or locking the data to protect it from unauthorized access. It makes the plaintext data gibberish that doesn’t make sense to the reader. The encrypted data looks like a string of random alphabets and digits. So, for example, if you encrypt the word “Hello,” it will seem like “n587ngw8y7356nhgiej39!”
Complex mathematical algorithms and digital keys are used to encrypt data. The only person having proper authorization such as a password, private key, secret code, session key, etc. can decrypt the data and read it.
So, what does encryption mean in terms of real-world applications? Encryption is used in many ways in real life. For example:
- All of the major search engines (like Google, Bing, Yahoo, etc.) encrypt your search queries and also the data they collect about you.
- All the third-party cloud storage platforms such as Google Drive, Dropbox, and Amazon AWS encrypt your stored data.
- Many encryption software applications are available (free and paid) in the market that offer the ability to encrypt personal files, photos, videos, contacts, wallet cards, notes, and audio recordings.
- Website owners use SSL/TLS certificates to facilitate the encryption of the data transferred between a website’s server and the website visitor’s browser.
- Software publishers use code signing certificates to encrypt the hash value of the downloadable software, drivers, and scripts to increase security.
- Companies use email signing certificates (S/MIME) or personal authentication certificates to sign and encrypt your messages in order to increase the security of your email communications
- A document signing certificate is useful for encrypting the content of files and documents.
- Organizations that fall within specific industries or handle specific types of data are subject to data privacy laws and regulations. For example, the Payment Card Industry Data Security Standards (PCI DSS), Health Insurance Portability and Accountability Act (HIPAA), and General Data Protection Regulation (GDPR) all require the encryption of individuals’ protected information.
What Does Encryption Do?
Now that you know that encryption hides the data from unintended users and protects it, the next question is how does encryption work?
Let’s explore this concept with Bob, Alice, and Mallory to understand encryption in a simpler way.
- Bob sends a letter to Alice. Mallory (the villain) gets access to the letter while it’s in transit. Because the letter is in plaintext, she can read, interpret, and even modify the message before it reaches Alice.
- To tackle this issue, Bob and Alice decide to use a trick. They will replace the original alphabet with its next to the next alphabet. That means A=C, B=D, C=E …. X=Z, Y=A, Z=B.
- Now, when Bob sends the message, “HELLO,” he writes, “JGNNQ” Instead.
- Now, if Mallory (or anyone else) gets access to the letter, all she’ll read is a bunch of text that doesn’t make any sense! But when Alice receives it, she knows the trick and shifts each letter of the message back two steps in the alphabet so she can interpret the message.
This is encryption in a nutshell! Now, let’s further explore some of the terms we used in this example.
A Breakdown of Terms Related to the Encryption Process
Ciphertext: The encoded text “JGNNQ” is called ciphertext. Basically, it’s the undecipherable text you get when you encrypt a message using an encryption algorithm and key. Ciphertext can only be decrypted using the corresponding key.
Encryption: The process of converting the plaintext “Hello” into a ciphertext “JGNNQ” is called encryption. Encryption is done using cryptographic keys which are made of mathematical algorithms. Encryption can be symmetric or asymmetric — and we’ll explain more about these two terms shortly.
Keys: The trick we referred to earlier about replacing individual letters within a message with those that are shifted one or two spaces in the alphabet is a generalization of what’s known as an encryption key. Bob is using it to encrypt the data, so it is an encryption key. Alice is using the same key to decrypt the ciphertext. That’s why it is also called the decryption key.
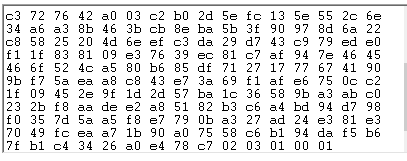
In real life, these keys are made of using mathematical algorithms. Some of the famous encryption algorithms are AES, RSA, Blowfish, ECC, Twofish, etc. The keys look like a long string of digits and alphabets. It looks something like this.
There are mainly two types of keys.
Symmetric key: When the same key is being used for encryption and decryption, it is called the symmetric key.
Asymmetric key: Here, there are two separate yet mathematically related keys are being used named public key and private key. The public key is available to everyone, and anyone can use it to encrypt the data. However, it has a unique pair of the private key, which must be kept in secret with its owner. Only the holder of this private key can decrypt the data. Sometimes, you need both, public key and private key to encrypt and decrypt the data.
Is It Possible to Break the Encryption?
In addition to asking what encryption is, people often wonder whether hackers can break the encryption. So, the answer is yes, it is possible. Modern encryption methods can be broken or “cracked” in two ways:
1) The Encryption Key Is Stolen or Leaked
The onus of success of this entire encryption is dependent upon the secrecy of the keys. In the symmetric encryption, the master key must be secured, and in asymmetric encryption, the private key must be kept secret.
If these keys are not kept secure and get leaked, any data that’s encrypted using those keys will become compromised. Anyone holding the required corresponding key can decrypt the data. Generally, in such an event, you need to immediately report your certificate authority to revoke your certificate and issue a new one.
2) The Cybercriminal Uses Bruce Force Attacks
The keys are made with a robust algorithm that’s nearly impossible for human brains to guess. For example, it requires 2256 different combinations to decrypt any text that has been encrypted with a 256-bit RSA algorithm. For computers, it would take 3.31 x 1056 years! However, with quantum computers, it seems possible to break such algorithms.
For example, the SHA-1 hashing algorithm used to be considered “impossible to break” before a couple of years. But it was broken by the experts with the help of supercomputers, and in the year 2017, all the browsers decided not to trust any certificates that use SHA-1.
How Much Does Encryption Cost?
Encryption is indeed a blessing for securing the stored data , which also helps to secure data while it’s in transit. So, how much does the encryption cost? If you are thinking that a technology that uses such high-class algorithms would cost you an arm and a leg, we have good news for you! The tools and certificates that facilitate the encryption are quite inexpensive. For example, a basic SSL/TLS certificate costs as little as $8.78/year. In the same way, an S/MIME or personal authentication certificate costs only $12.95/year.
If you’re an individual who wants to use encryption, there are many free or low-cost encryption tools available in the market that encrypt documents, files, images, and other media content. These tools are highly recommended for freelancers and remote workers to securely transfer and store their professional work.
What Does Encryption Do in an SSL/TLS Certificate?
An SSL certificate is used to protect data that are transmitted between two endpoints, generally a website and the website visitor’s browser. Let’s break down how that process works with an example:
How Keys Are Allocated
- Let’s say you’re a website owner and you buy an SSL certificate for your domain(s). You need to initiate a process known as a certificate signing request (CSR) on the server where the website is hosted.
- The server generates two mathematically related unique keys called the public key and private key.
- You need to send the public key to the certificate authority (CA).
- After successful validation, the CA issues an SSL certificate for the domain, ties its public key to the certificate and signs it with its own intermediate root certificate.
How to Transfer Data Using Asymmetric and Symmetric Encryption Simultaneously
- Now, every time a user visits your website, their browser generates a session key and encrypts it using the public key attached to the website’s SSL/TLS certificate.
- The session key reaches the intended website’s server. Only the intended server can decrypt the session using the corresponding private key.
- Now, this symmetric session key is used for encrypting and decrypting all of the data that transfers between your server and the user’s browser.
As you can see, the data traveling between your website and browser remains encrypted while it is traveling using unsecured internet. Anyone can intercept this data. But when it is encrypted, the perpetrator can’t read, interpret, steal, or modify it. To do so, they need the session key to decrypt the data.
However, the session key itself is encrypted and can be decrypted by the private key, which only the intended website has. It is impossible to get access to the session key without a private key. Hence, the data you send over a website gets two layers of protection. This is how an SSL/TLS certificate protects your website’s visitors’ data from the man-in-the-middle attacks, session hijacking, data theft, eavesdropping, and other sorts of online dangers.
How Does Encryption Work in Personal Authentication Certificates?
Sometimes, the encryption is done using both types of encryption keys (i.e., a public and private key) simultaneously. Some of the email signing certificates and personal authentication certificates (PAC) work in this way. Let’s use Bob and Alice’s example to understand the process flow when two email clients have installed an S/MIME certificate:
- When Bob sends an email to Alice, Bob’s email client encrypts the email contents using Alice’s public key.
- When such an encrypted message reaches Alice’s email client, Alice only needs her own private key, which her email client will use to decrypt the message. As Bob uses Alice’s email client’s public key to encrypt the data, only its corresponding private key can decrypt it. Only Alice has access to this private key.
- Now, Alice responds and encrypts her message by using her email client’s private key and Bob’s public keys.
In this way, the entire conversation will be encrypted, and only the intended person’s email client can decrypt it.
Wrapping Up Our Explanation of “What Is Encryption”
Now, more and more companies and government organizations are becoming paperless and shifting their data online. This data contains financial information, personal details, healthcare related data, company’s trade secrets and even confidential political data. When you transfer or store such sensitive information online, it’s security must be a top priority. If such confidential data gets leaked, many types of crimes such as identity theft, financial fraud, ransomware attacks, etc. can cause dire consequences for individuals, businesses, and governments.
Encryption is one of the best ways to secure sensitive data. When someone intercepts encrypted data, they can’t interpret it or use it for their own purposes. We hope this article helped you to understand how encryption works in a better way.














 (34 votes, average: 4.79 out of 5)
(34 votes, average: 4.79 out of 5)






2018 Top 100 Ecommerce Retailers Benchmark Study
in Web Security5 Ridiculous (But Real) Reasons IoT Security is Critical
in IoTComodo CA is now Sectigo: FAQs
in SectigoStore8 Crucial Tips To Secure Your WordPress Website
in WordPress SecurityWhat is Always on SSL (AOSSL) and Why Do All Websites Need It?
in Encryption Web SecurityHow to Install SSL Certificates on WordPress: The Ultimate Migration Guide
in Encryption Web Security WordPress SecurityThe 7 Biggest Data Breaches of All Time
in Web SecurityHashing vs Encryption — The Big Players of the Cyber Security World
in EncryptionHow to Tell If a Website is Legit in 10 Easy Steps
in Web SecurityWhat Is OWASP? What Are the OWASP Top 10 Vulnerabilities?
in Web Security