A Look at Session Hijacking Attacks: Session Hijacking Explained
After four long years, OWASP released their new list of the top 10 web application security threat categories. This list includes XSS injections and session fixation attacks, both of which are considered session hijacking attack methods. Let’s explore what session hijacking is and why it matters to your organization
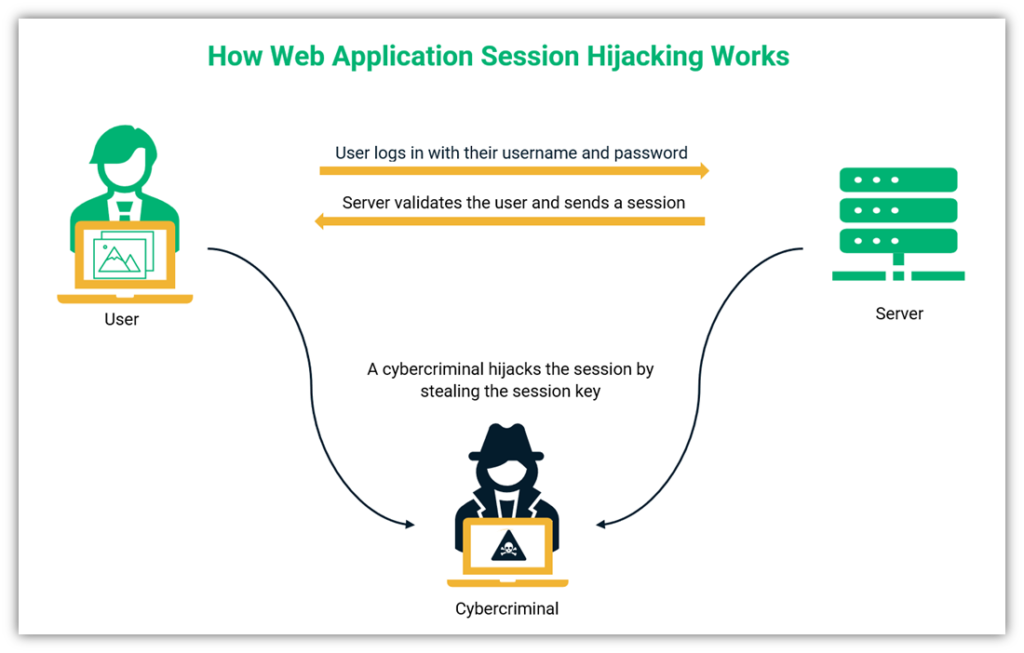
A visual representation of session hijacking or cookie jacking where the cookies used by a web application are hacked by cybercriminals. (Made using Canva)
Thousands of Facebook accounts have been compromised since March 2021 due to a session hijacking malware called FlyTrap. FlyTrap spread across 10,000 victims as an Android Trojan. The malware could collect a variety of victims’ data, including:
- Facebook IDs
- Locations
- Email addresses
- IP addresses
- Cookies and Tokens associated with Facebook accounts
These hijacked sessions were used to spread malware and disinformation by abusing the victim’s social credibility. But what is a session hijacking and how does it work? Why is it a threat to your business and customers? And what can you do to prevent session hijacking attacks?
What Is Session Hijacking?

In the most general terms, session hijacking, or “session sidejacking” is a type of cyber attack that involves an attacker taking over or “hijacking” your active web session. (A session is your connection to a website — like when you log on to pay bills or check your email.) Bad guys can do this by stealing or even guessing the unique identifier (i.e., a cookie or a string of numbers) that a website has assigned to your session to pretend that they’re you.
What session hijacking does is give the bad guy unauthorized access to the site as you, meaning that they can see everything relating to your account. This includes everything from seeing your personal or payment card-related information to performing fraudulent activities in your name. A session hijacking attack can occur in real time, or an attacker can use the session ID to impersonate you at a time that’s more convenient for them.
Session hijacking can occur in several ways (which we’ll speak about more in-depth in a few moments). However, these types of cyber attacks typically fall into one of two categories:
- Web application attacks. This first category, which is what we’ll mainly focus on in this article, revolves around cybercriminals stealing your identifying token (such as a cookie, a string of numbers that uniquely identifies you to the website) when you first connect to a website. This is why these types of session hijacking are also sometimes known as cookie stealing or cookie hijacking.
- Network layer attacks. This second category, also known as TCP session hijacking, works on the transport layer. This process involves stealing data packets while they’re transmitting from your device to the website’s server.
Why Session Hijacking Is Dangerous for Users and Businesses
To understand the dangers of session hijacking and why it’s such a threat to your users and organization, let’s consider the following scenario.
Say you have an eCommerce website. If a criminal gets ahold of the session ID of your employee or any other user, they can do one or more of the following (depending on which account they can access):
- View or change the user’s account information (they can view personal information, payment account information, change the user’s login credentials, etc.).
- Make fraudulent purchases or other transactions (such as money transfers) on behalf of that user.
- Access secure company resources and steal data, which can result in a data breach.
The results of the data breach are catastrophic. IBM reported some interesting results after conducting research on the data breach. Some of the findings include the following:
- The average cost of a data breach increased 10%, from $3.86 million in 2020 to $4.24 million in 2021.
- These data breach costs represent the largest year-over-year increase in the last seven years.
- A cost difference of $1.07 million was observed when remote work was a factor in the data breach.
- 38% of the cost of a data breach could be attributed to loss of business.
- Personally identifiable information (PII) costs an average of $180 per record.
- 20% of the breaches had compromised credentials as the initial attack vector.
Like the rest of us in cyber security, IBM is rooting for organizations to achieve higher standards in security AI and automation, zero trust, and cloud security to reduce the costs associated with data breaches. But in order to achieve higher security, organizations need to understand the various types of threats that exist.
Session Hijacking vs. Session Spoofing
Session hijacking and session spoofing are both types of attacks where a cybercriminal takes over a victim’s session. The principal difference between session hijacking and session spoofing is the timing of the attack. In session hijacking, a criminal will carry out the attack when the victim is logged in on the system. While in session spoofing, the attacker will log in to the victim’s account with the help of stolen credentials when the victim is not logged in.
How Session Hijacking Works
A cybercriminal can hijack the session of the victim by stealing the session ID or a session cookie to make the server believe that the criminal is the legitimate user. The bad guys can also hijack the session by persuading the victim to log in using a compromised session ID. There are mainly two ways in which the cybercriminal can carry out these attacks:
- By installing malicious software on the victim’s device, or
- By sending out phishing emails and tricking the victims into logging in.
Of course, session hijacking attacks can be carried out in different ways. Let’s look at them in more detail.
How Web Application Session Hijacking Works
Generally, web application session hijacking involves the criminal stealing the target’s session ID or their session cookie by sending out phishing emails/links to the victim. Once the victim logs in using this link, the criminal is in and will be able to read or change the information transmitted.
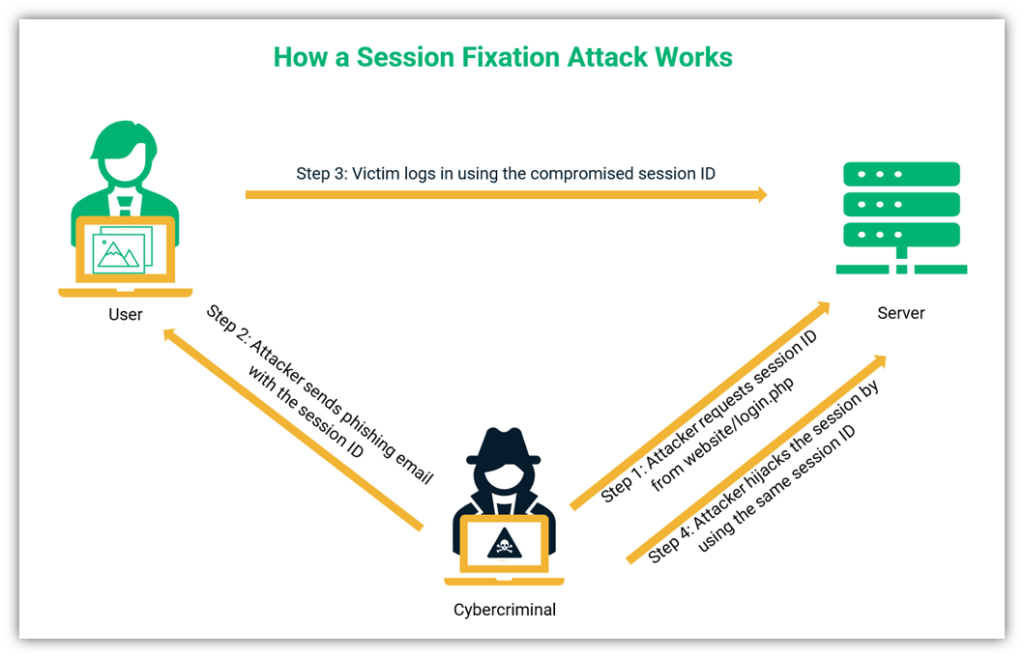
The following figure is a representation of how web application session hijacking works:
So, what exactly are session, session key, and cookie? How do they impact the session hijacking scenario?
A Web App Session Is Like Using a Valet Service… You Don’t Want Your Keys in the Wrong Hands
Let’s understand everything with the help of an example. If you go to a restaurant and use their valet service to park your car, you hire the service for a short bracket of time. It can be compared to the session you have online. Essentially, a session is a time slot assigned to a specific user where the server will remember all their activities and will track different connections of the same user.
Continuing the example, when you ask a valet to park your car, he will take your car and give you a token. This token is not your actual car, but the valet will return your car once you show him your token. The valet will hand over your car to anybody who has that specific token.
Technically, a session key or token is a unique ID consisting of alphanumeric characters that identify the session. When the user makes requests to the server, this session key is used as a reference. It is akin to the unique ID on the token you receive from the valet service for your car.
An internet cookie, or the HTTP cookie, is like a valet token in this scenario. As the valet token contains the details about your car, including its registration number, a cookie contains all the details of your online session. You can retrieve your car by presenting the token to the valet service.
The following figure represents the relationship between the session, session key, and cookie:
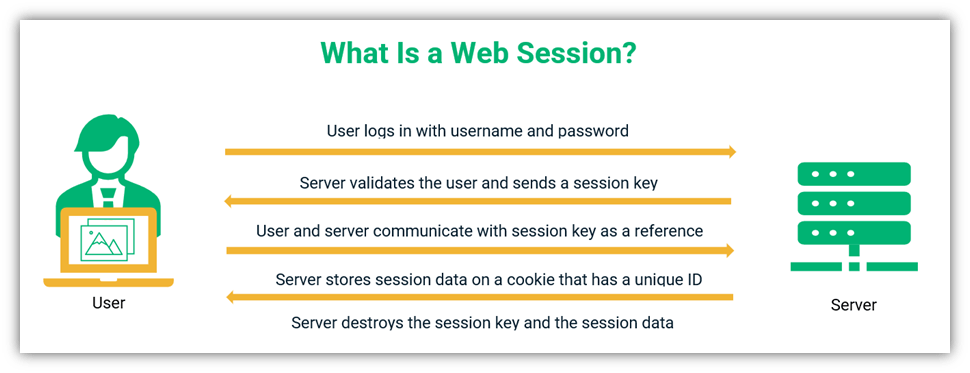
Moreover, it doesn’t matter who presents the token; the valet will give access to your car to that person. This means that if a cybercriminal gets ahold of your cookie, the server would not be able to differentiate them from you, so they’ll share the session details with them. This process would give the attacker access to your account and the ability to perform actions that you normally would as a legitimate user.
How TCP Session Hijacking Works
TCP session hijacking involves an attacker inserting malicious code to impersonate a victim’s device. Once such code is inserted, the server will consider the attacker as the legitimate user. For understanding TCP session hijacking, it is important to know what TCP is and how it works.
What Is TCP?
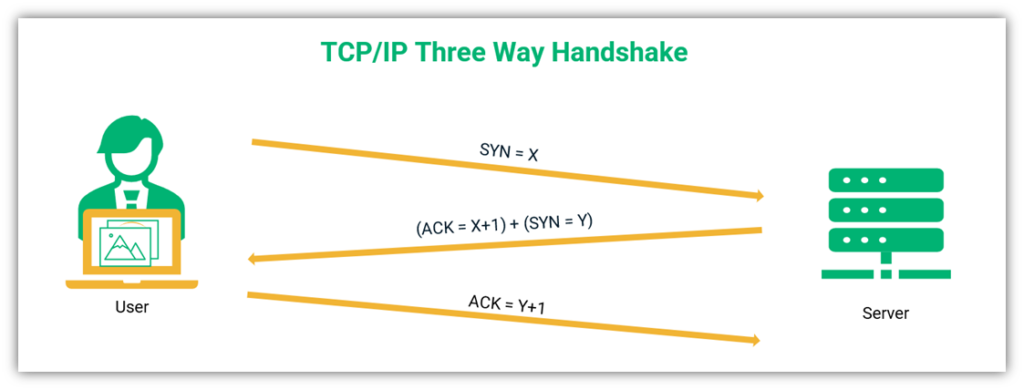
The transmission control protocol (TCP) is a protocol used in addition to the internet protocol (IP) to transfer the data packets reliably. TCP facilitates maintaining lost packets, duplicate or corrupted packets, and out-of-order packets while transporting the data packets.
TCP uses a three-way handshake to connect user and server. The user will send a random number (X) to the server. The server will acknowledge it by adding 1 to the random number (X+1) and will add a random number of its own (Y). The client will acknowledge it by adding 1 to that number (Y+1). The following figure shows this three-way handshake:
A cybercriminal might place himself on the port used by TCP/IP to sniff the source-routed IP packets at the network level. They will respond to the server with the correct ACK message. The server will consider the reply as coming from the legitimate user and grant access to the attacker. The MitM attacker will hijack the session without the server ever knowing about it. The following figure shows how the attacker can hijack the session using TCP:
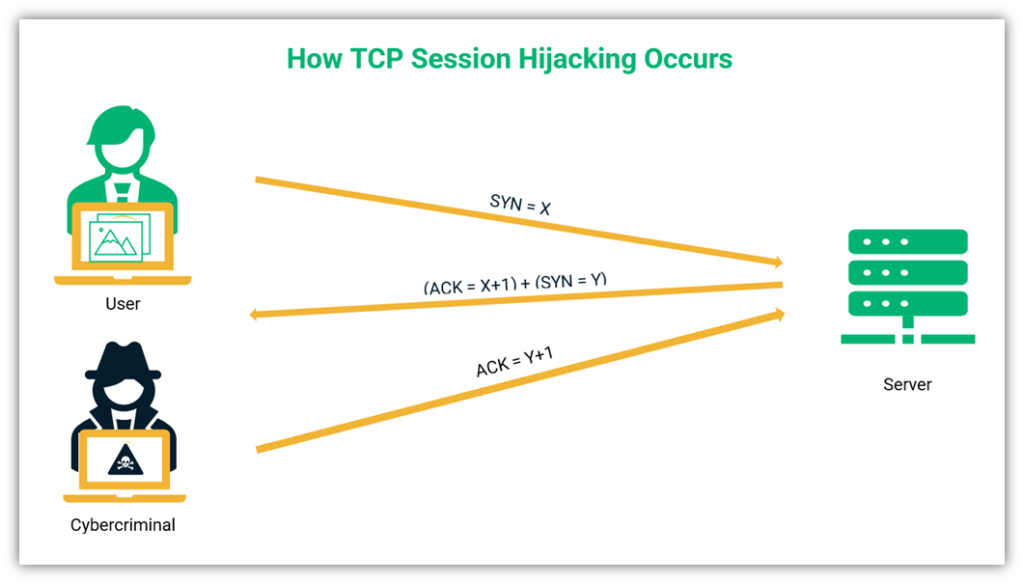
For TCP session hijacking, the criminal needs to know the TCP and IP headers and packet payloads. Therefore, they use a method called ARP poisoning. The following video explains the man-in-the-middle attack by ARP (Address resolution protocol) poisoning in a simple way:
3 Methods of Session Hijacking (And 1 Closely Related Attack Method)
A cybercriminal can use various methods to hijack your session. They can also use a combination of methods to carry out a session hijacking attack. Let’s look at some of the most commonly used methods of session hijacking as well as some other closely related attack methods.
1. Session Sidejacking
Session sidejacking is a method of session hijacking where an attacker sniffs the traffic for session cookies on an unencrypted communication channel. Once they find cookies, they can use them to impersonate the victim and hijack their session.
An attacker can easily set up a Wi-Fi network and offer it for free. Some criminals name these free Wi-Fi networks with names that sound authentic, like “Baer County Free Wi-Fi” or “AT&T Free Wi-Fi” to attract potential victims. The unsuspecting users will start using this Wi-Fi and browse the internet. Many outlets genuinely offer free Wi-Fi to their customers, but they cannot control who logs in.
Criminals treat these open Wi-Fi networks as bait to attract and ensnare victims. As soon as the victims log on to websites that only have their login pages covered and click on the unsecured page, the criminals can sniff them and hijack their session.
The method in which the cybercriminal sniffs the data packets transferred between two nodes on the internet to steal the session cookie is called session side jacking or session sniffing. Open wireless networks or hotspots help criminals lure users to their network, and unsecured websites help them to steal users’ session cookies.
2. Cross-Site Scripting XSS
A cross-site scripting (XSS) attack tricks the system into executing malicious code by concealing it in the trusted server. The device will execute this malicious code, assuming it to be safe. However, this code helps the attacker to steal cookies.
According to Edgescan, cross-site scripting (XSS) was the leading reason behind high-risk security vulnerabilities (37.2%) in application security in 2020. The method of session hijacking targeting the vulnerabilities in web applications is known as cross-site scripting or XSS. A criminal deceives the client device into running a malicious code that appears to be a legitimate server code. When the client device runs this code, the criminal gets a foothold on the device, allowing him to obtain the cookies and hijack the session.
All major browsers have a basic security feature called the same-origin policy (SOP), so the websites can only access codes from the same origin. The browser will consider URLs with the same URL scheme, hostname, and port number to be from the same origin and share the permission among them.
A cross-site scripting (XSS) attack is more than just a method of session hijacking. XSS attacks inject malicious code, generally JavaScript, into vulnerable web pages processed by the user’s client (browser) by exploiting server and application vulnerabilities. Because the browser trusts that the page’s codes are legitimate, it’ll then share sensitive data. This will allow cybercriminals to hijack the session and steal sensitive information.
The following video is an excellent explanation to XSS:
3. Session Hijacking Using Brute Force
Sometimes, the session ID uses predictable variables like the user’s IP address along with the date and time of user login. Cybercriminals can guess these kinds of identifiable patterns by carrying out a brute force attack.
A brute force attack is a method that cybercriminals use to bypass traditional login methods and force their way into an account. They do this by repeatedly attempting to log in by guessing username-password combinations. The same concept applies here to session IDs for session hijacking — an attacker can try their hand at guessing session IDs until they find one that works. When shorter session IDs are used, brute force attacks become simpler to perform.
Session Fixation
Although session fixation attacks are closely related to session hijacking, it is slightly different from the session hijacking attacks. A session fixation attack is a cyber attack where the criminal gains access to the user session by luring the victim into logging in on a website using a compromised session ID.
Session fixation attacks are carried out by taking advantage of a security mechanism vulnerability that allows one person to set (fixate) the session ID for another person. It can occur in one of several ways depending on how your site is coded and organized.
Session Fixation Method One: Stealing a User’s Session ID
A criminal might send a phishing email to the victim containing the link that contains a session ID. When the victim clicks on the link, they will see a familiar login page. When they enter their credentials, the attacker will be able to know the sessions ID used. The attacker will be able to carry out all the functions the victim could do on his account.
Let’s compare it to the valet metaphor. A bad guy can dress up as the valet, and you will give him the token of your car parked earlier. The attacker will take the token and go to the real valet, who will hand over your car to him, thinking it’s the legitimate owner (you). Your car will be stolen with a compromised token.
Session Fixation Method Two: Stealing Users’ Login Credentials
Let’s explore another way in which a session fixation attack can work:
- The attacker goes on the targeted website.
- The website sends a legitimate session ID to the attacker.
- The attacker will send the same session ID to the victim via a phishing link. However, instead of sending them to the legitimate website, they’ll divert the victim to a fake site.
- Because the fake site is designed to look legitimate, the victim logs in to their account thinking that the phishing site is real.
- The attacker will collect the login credentials from the fake site and log in as the victim on the original site impersonating the victim. Thus, allowing the attack to fixate the session.
Session Fixation Method Three: Using a Phony Subdomain
The third way to carry out session fixation is when an untrusted site gives out its subdomains to a fishy third party (attacker). The attacker will lure the victim into using this website. When the victim logs in, a session cookie is created on the victim’s browser. The attacker accesses the cookie from the subdomain by sending a request. The attacker thus gains access to the victim’s account for that session.
This method is harder for an attacker to pull off because they’d need to have access to a domain’s subdomain.
How to Prevent Session Hijacking Attacks
Isn’t it scary to see so many methods used for session hijacking? However, implementing preventive and security measures can help you secure your session. Cybercriminals take different routes for each session hijacking method; hence, security experts must devise different measures to foil their attacks and put a stop to these threats.
Use Encryption on Your Website (Enable HTTPS)
The most reliable method to have secure communication on an untrusted network is to use SSL/TLS encryption. Many website owners buy SSL certificates only for their login page. Other pages or subdomains on the website are unprotected.
Encryption is the key (pun intended) to secure online communication. SSL/TLS certificates should be used on the entire site to encrypt all data traffic between the client and the server — everything from your primary domain to your least trafficked subdomains.
Some web owners make a mistake in securing only the login pages. This leaves your whole website vulnerable to attack and your data open to exposure or compromise. To avoid these issues, enable HTTPS across your entire site.
Implement Session ID Hygiene
If you follow certain rules at the time of generating session ID, the attackers will have a hard time cracking it. The following steps will help you have better session ID hygiene:
- Use random session IDs instead of following a particular pattern to generate session IDs.
- Regenerate session ID after each login to prevent session fixation or spoofing.
- Accept server-generated session IDs only. Don’t accept session IDs from any other source.
- Use long session IDs to prevent brute force attempts for session hijacking.
- Never use session ID in URLs or POST variables.
- Implement time-outs for inactive sessions to reduce the chances of hacking. A new session ID can be generated the next time you log in.
Another option recommended by OWASP’s Session Management Cheat Sheet is to bind specific identifying characters or user properties to the session ID to help prevent unauthorized access:
“If the web application detects any change or anomaly between these different properties in the middle of an established session, this is a very good indicator of session manipulation and hijacking attempts, and this simple fact can be used to alert and/or terminate the suspicious session.”
Practice Good Cookie Security Hygiene
If you follow some practical rules for maintaining cookies, you can have a higher level of security. Let’s look at how you can secure your “cookie jar” against attackers:
- Use HTTPS to send cookies. The application server can set the secure cookie flag when a new cookie is sent to ensure that the browser sends cookies via HTTPS only (not via the insecure HTTP protocol).
- Use unique cookies for each request. Configure cookie values to change after every request. Practically, this means a new cookie is created after every request, and the attacker might not have enough window to launch an attack.
Ensure Website Users Follow Security Hygiene
If you are a website user, you should follow some practices to protect your website sessions from session hijacking attacks:
- Don’t click on suspicious links from emails or other sources.
- Delete suspicious emails and text messages with follow links.
- Check the referrer header and delete the session if you find anything suspicious. When you visit a website, the browser will set a referrer header that contains the link to the site you visited. If you check the referrer header and find inconsistency in the link, you should delete your session at once.
- Never leave your device unattended or unlocked when it’s not in use or within your physical possession.
- Enable two-factor authentication (2FA) or multi-factor authentication (MFA) on your accounts for added security.
- Use anti-malware software and a firewall to protect your endpoint devices and network from attackers.
- Avoid using unknown and public wireless networks.
- Don’t use insecure websites (i.e., websites lacking HTTPS in the browser’s address bar).
Final Words on Session Hijacking
A cybercriminal can do virtually anything a victim can do by hijacking the victim’s session. The server will consider the attacker as a legitimate user. An attacker can steal money (carry out the transfer from his bank account) or steal sensitive information. When the criminals get access to the victim’s personally identifiable information (PII), they can carry out identity theft.
There are several ways in which a criminal can hijack a session. You can protect your IT systems only by following a strict security regimen.





















2018 Top 100 Ecommerce Retailers Benchmark Study
in Web Security5 Ridiculous (But Real) Reasons IoT Security is Critical
in IoTComodo CA is now Sectigo: FAQs
in SectigoStore8 Crucial Tips To Secure Your WordPress Website
in WordPress SecurityWhat is Always on SSL (AOSSL) and Why Do All Websites Need It?
in Encryption Web SecurityHow to Install SSL Certificates on WordPress: The Ultimate Migration Guide
in Encryption Web Security WordPress SecurityThe 7 Biggest Data Breaches of All Time
in Web SecurityHashing vs Encryption — The Big Players of the Cyber Security World
in EncryptionHow to Tell If a Website is Legit in 10 Easy Steps
in Web SecurityWhat Is OWASP? What Are the OWASP Top 10 Vulnerabilities?
in Web Security