What is Multi Factor Authentication and How Does It Differ from 2FA & SFA?
Explore the differences between MFA, 2FA, and SFA — how each is used, and what they mean for your organization and customers
Wondering “what is multi factor authentication?” or “what is two factor authentication?”
You’re likely here because you’ve heard of multi factor authentication (MFA) and/or two factor authentication (sometimes written as 2FA or 2 factor authentication) and want to know what they are and what they do. In a nutshell, they’re both security processes in which a user has to verify their identity to protect their credentials and the information they wish to access. These authentication methods are increasingly being used by email and banking apps.
But, wait, aren’t MFA and 2FA the same? Not quite. Oh, and there’s a third authentication method I haven’t really touched on yet — single factor authentication. (I’ll get to that in a bit.)
In this article, I’ll break down:
- What multi factor, two factor, and single factor authentication are individually,
- How they differ from each other, and
- How to choose one method over the others.
What is Multi Factor Authentication?
Multi factor authentication (sometimes written MFA) is a verification process that involves a user proving they are who they say they are with multiple methods — before your organization allows them to access their account. Not sure how multi authentication works? The specific authentication methods vary, but in general, they usually fall within the following three categories:
- Something you know. This type of information (what Imperva refers to as a “knowledge factor”) can be a password, passphrase, a security question response, or another piece of specific information that authenticates you.
- Something you have. This category of info (what Imperva refers to as a “possession factor”) includes something you have in your possession. A few examples are a USB security token, a common access card (CAC) reader, or even a mobile app on your personal or company device.
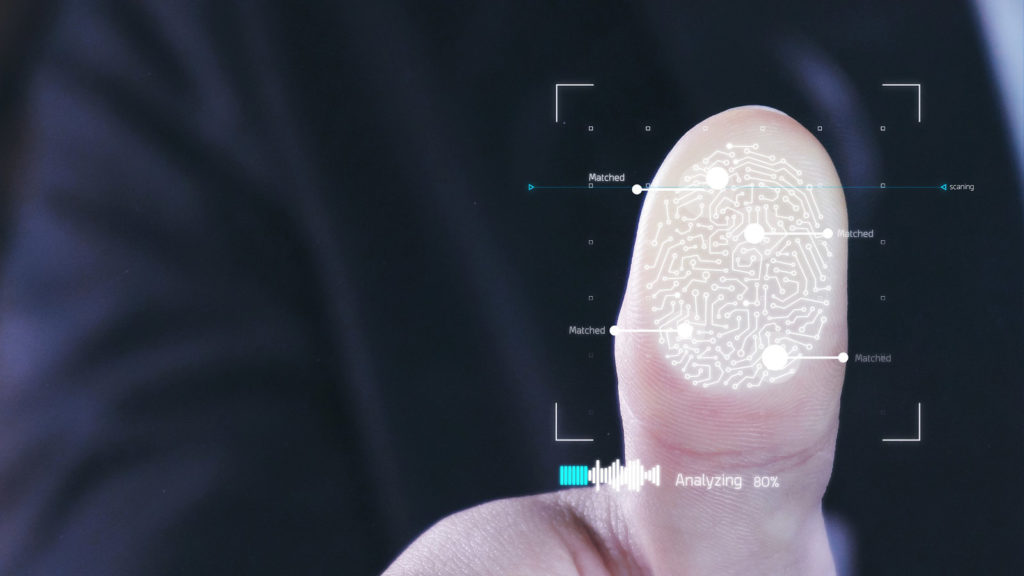
- Something you are. This type of data (which Imperva refers to as an “inheritance factor”) can be a type of biometric information — for example, a fingerprint, retinal scan, facial recognition scan, or even a voice sample.
With multi factor authentication in place, a user would have to meet two or more of these identifying criteria. For example, they may need to not only have an item in their possession, but they’d also need to know a password, PIN, or another piece of information. Or they may need to have their phone and would need to biometrically prove their identity with a physical attribute.
What is Two Factor Authentication?
Two factor authentication is also a verification security process— but it’s not as stringent. 2FA only requires two of these forms of identification. But, wait, doesn’t that mean that MFA and 2FA are the same after all? Nope. Because 2FA is multi factor authentication, but not all multi factor authentication is 2FA. It’s kind of like food — all types of mac & cheese are food, but not all foods are mac & cheese.
How about a real-world example? A perfect example of two factor authentication is when you use a debit card at an ATM machine. Not only do you need to be in possession of the card (what you have), but you also need to know the PIN (what you know) that’s associated with the card to use it.
Whenever I log in to my mobile banking app using my username and password, I’m prompted to enter a six-digit verification code that I receive via an SMS text message on my phone or via an email. To access the account, I need to enter the code within a specific amount of time — otherwise, the code expires and then I have to start over. The same process is required when users opt-in to using Google’s 2-Step Verification method to protect their accounts.
What is Single Factor Authentication?
Well, now that we’ve gone through the other two categories, you can see that “single factor authentication” is a term that’s self-explanatory. A single factor authentication method is one that simply requires a user’s password to compromise their account. For example, if you use “admin” as both your username and password, then you’re essentially handing over your information and accounts to cybercriminals. It’s the most basic and insecure method of account protection that, realistically, amounts to a whole lot of nothing!
Password cracking tools, password databases from data breaches, and brute force attacks make account compromises easier for criminals. However, if you use a complicated password — one that contains a combination of uppercase and lowercase numbers, letters, and symbols — then hackers will have a lot more difficulty trying to force their way into your account. Some tools enable hackers to crack simple passwords like “admin” or “password” within seconds.
Don’t make it easy for criminals — make ‘em work for it! Cause them to fail time and again by using complicated login credentials they can’t guess easily. The more challenging you make it to break into your account, the more likely criminals will be to simply give up and move on to other (easier) targets.
How Do You Choose Between MFA, 2FA, and SFA Authentication Methods?
Now that we’ve answered your questions about “what is multi factor authentication?” and “what is two factor authentication?” we can move on to your next burning question: How do you choose between them?
The answer ultimately depends on the security needs of your business and customers. Ask yourself the following question: If someone was able to access your account, how damaging would it be? Could they get payment details or otherwise cause significant damage? If not, you may be fine with SFA. After all, you don’t want to risk needlessly annoying customers with what they may perceive as “too much” security where it’s not needed. This can result in a cumbersome or frustrating experience for them.
Critical websites, apps, or services that handle any type of personal or financial information (such as banks, email service providers, healthcare providers, and credit agencies) should make the multi factor authentication process mandatory. For other websites that handle non-critical personal information, two factor authentication should provide ample data security.
But these authentication mechanisms must be costly for businesses to implement such a security mechanism at scale, right? After all, there would be hardware and logistical costs to consider — not to mention password, support, or help desk-related costs…
Please. Don’t use price as a cop-out. I think we can agree that data security is invaluable. After all, once your system is breached and the information is out there, you can’t unscramble that egg. So, do you want to pay the costs up-front by getting your ducks in a row and systems in place? Or, do you want to pay significantly higher costs after-the-fact when the proverbial manure hits the fan, your brand reputation takes a hit, and you’re slapped with fines and lawsuits?
The choice is yours. But I’d recommend taking option No. 1 and save yourself — and your customers — a plethora of headaches and costs in the future. Especially when those costs are ones that you could have been avoided.
























 (12 votes, average: 3.67 out of 5)
(12 votes, average: 3.67 out of 5)





No comments