12 Network Security Best Practices to Secure Your Business
Put these 12 simple network security best practices into action now to secure your digital environment
For any organization across any industry vertical, network security best practices and basics must come into play if cyber attacks are to be prevented, detected, or mitigated. Network security is a combination of essential security activities and policies that are designed to assess, monitor, and manage the network promptly in matters of security threats, unauthorized intrusion, etc.
In the following sections, we’ll explore some network security best practices that you can implement to secure your corporate network.
The Top 12 Network Security Best Practices
Most of the net security best practices described below are generic and widely implemented — they also can be adopted irrespective of your specific network design. Having said that, network security best practices include but are not limited to the following tips. Furthermore, you should consult with your security architect to explore other controls you can implement specific to your network architecture.
Network Security Basics Tip 1: Know Your Network Infrastructure
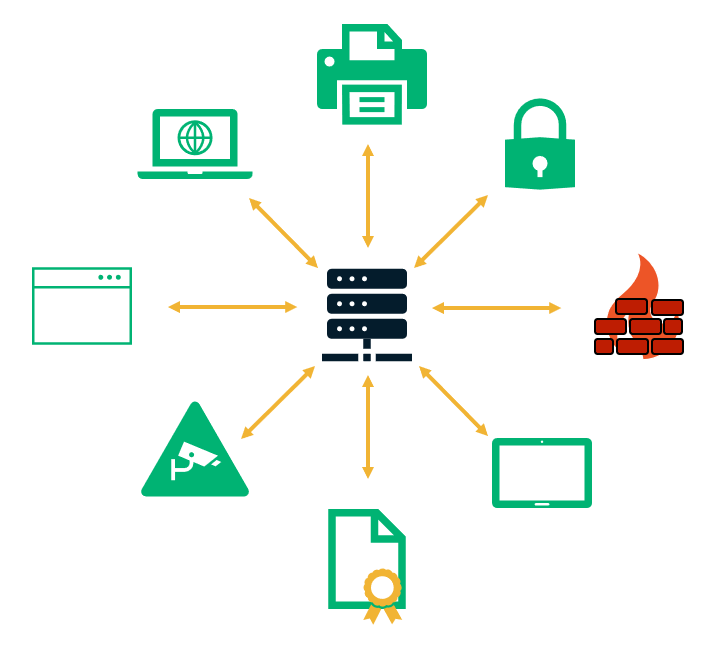
Having visibility into your network infrastructure is crucial before you can even begin to secure your network against potential threats. Unless you know which hardware/software devices components comprise your network, you won’t be able to protect them.
When formulating your network security strategy, you should take into account all your:
- Hardware (routers, switches, printers, etc.)
- Software (firewalls, IDS/IPS, etc.) devices, and
- Digital security certificates (SSL/TLS certificates, IoT certificates, etc.).
Network Security Basics Tip 2: Implement Network Segmentation and Segregation Strategies
Handling security for a sizeable unsegmented network (with tasks such as defining firewall policies and effectively managing how the traffic flows) can be a complicated business. Segmenting your network into smaller chunks and establishing different trust zones can not only makes management easier but can also keep networks isolated in the event of a security incident, reducing the risks and impact of a network intrusion.
An unsegmented network provides potential hackers with a larger attack surface where they can move laterally through the network to access business-critical data. Such a breach can evade detection owing to the enormity of the network. Implementing network segmentation and segregation proves useful in such scenarios, giving you the control over how traffic moves within your environment.
Network Security Basics Tip 3: Opt for a Data Loss Prevention Solution
Data exfiltration, or the unauthorized movement of data from an endpoint (either due to malware or insider threats), is a common occurrence within an organization. If your organization stores, processes, or transmits sensitive data (such as personally identifiable information [PII], payment card industry [PCI] data, client data, etc.), it may be subject to compliance regulation that makes it mandatory to protect such data. Irrespective of regulatory requirements, it makes sense to identify and keep track of events surrounding critical data to avoid any breaches.
Network Security Basics Tip 4: Conduct Awareness Training for Users and Staff

Insider threats often emerge in the form of negligent employees who’re unaware of network security best practices when it comes to maintaining good cybersecurity hygiene. While employees can be the easiest targets for attackers via social engineering techniques and phishing emails, they can also prove to be your best defense against potential security breaches.
Infosecinstitute.com reports that in a study of an unnamed Fortune 50 organization, where 35% of the employees received training to identify fraudulent emails based on a simulated phishing attack, the training led to an 84% decrease in the chances of falling victim to such attacks.
Offering mandatory organization-wide cyber awareness programs, particularly when done on a regular basis, drives home the importance of network security basics, IT compliance, password security, etc. It also ensures that employees stay informed about different forms of cybersecurity threats.
Network Security Basics Tip 5: Conduct Third-Party Vendor Assessment
Working with third-party contractors may be unavoidable in some cases. However, if they’re given access to your business network, it has an impact on the overall security of your organization. Because it increases the number of access points to your network, ensure that the security posture of these third-party vendors is carefully evaluated based on the level of access they require.
For instance, Airbus was attacked at least four times last year via its third-party supplier networks — Rolls Royce, Expleo, and two others, according to bitsite.com. Hackers targeted virtual private networks to gain remote access to their business network in search of intellectual property of the aerospace manufacturer. Similarly, in the past, Target and several other organizations have fallen victim to attacks via external vendors.
Network Security Basics Tip 6: Establish an Incident Management Plan
An incident management plan provides guidance for how you can get your business from managing a cyber incident to when you return to normal operations. It provides structure and the necessary information your incident management and incident response teams need to do their jobs.
When an incident response plan is put into action, the incident response (IR) team comes into the picture in the event of a security breach that’s detected by means of network security monitoring. They’re responsible for escalating the incident to the appropriate teams and work on a timely resolution. Once the situation resolves, the next step is to recover systems to restore their proper functioning. A business continuity/disaster recovery plan can go a long way to ensure the availability of your network and associated systems.
The National Institute of Standards and Technology’s (NIST) Computer Security Incident Handling Guide (800-61) also provides some great information regarding computer security incident response.
Network Security Basics Tip 7: Administer Regular Software Updates and Patch Management
Did you know that 27% of reported breaches were the result of unpatched vulnerabilities? Data from Tripwire, a security company, also indicates that unpatched vulnerabilities were also responsible for 34% of data breaches for European organizations.
Updating and patching up software is crucial to preventing exploitation via any known vulnerabilities in applications developed in-house or through proprietary software. Be sure to install available security patches and updates for all your software within a targeted timeframe that’s in line with the entire organization’s risk management process.
Network Security Basics Tip 8: Validate the Security of Network Devices
All efforts to secure your network will be in vain if there are glaring security loopholes or bugs in your connected network devices. Ask yourself: How secure are the devices that have access to your network? There are a few key things to consider:
- All network devices (servers, desktops, routers, etc.) should only be purchased from authorized resellers and well-reputed vendors.
- Also be sure to configure devices securely to turn off unnecessary services, disable unassigned or unused ports, manage default settings, etc.
- When updating your network equipment devices, make sure that patches are downloaded only from validated sources.
Network Security Basics Tip 9: Protect Your Network Against Malware

Phishing scams are on the rise, and one can never be too careful when it comes to malware protection. Installing an endpoint protection solution (which typically includes anti-malware) on all your network’s endpoints establishes a consistent, standardized, and distributed layer of security along your network perimeter.
Another way to protect your network from malware is to use email signing certificates/personal authentication certificates (PACs) for your email clients. If all of your employees are using these digital certificates, which attach digital signatures to every email, it helps to ensure that your employees can verify whether someone in your business really sent any questionable or suspicious emails.
Network Security Basics Tip 10: Formulate an IT Policy and Enforce It
Clearly defined IT policies not only act as directives that empower your employees as they carry out their duties, but they also hold them accountable in case of non-compliance. A network security policy governs how to implement and maintain security across the computer network. It outlines rules for access, operation, etc. under ordinary conditions and offers guidance on how to proceed in the event of a breach.
To enforce such policies, however, you need to ensure that your employees are aware of them. Data from a Kaspersky Labs study indicates that only 12% of surveyed employees claim to know their organizations’ IT security policies and requirements. These rules and policies should be part of not only the onboarding process, but they also should be included in regular cyber awareness trainings to keep them top of mind.
Network Security Basics Tip 11: Deploy the Right Technology
There are several network security solutions that you’d want to take into consideration in terms of tools that need to be deployed to secure your environment. Some of these include:
- Intrusion detection systems/intrusion prevention systems (IDS/IPS),
- Firewalls,
- Virtual private networks (VPNs),
- Unified threat management (UTM) tools, and
- User and entity behavior analytics (UEBA) solutions.
Choose your technology in a way that they interoperate cohesively, especially in cases where the technology comes from various vendors. The network intelligence gained from a security device should be usable by other devices since operating in silos can have a negative impact on event correlation and analysis.
Network Security Basics Tip 12: Assemble the Right Security Team and Keep Their Skills Current

According to Cybersecurity Ventures, by 2021, there will be 3.5 million unfilled jobs in the security industry with an ever-increasing skill gap. As several organizations compete to hire security professionals from a limited resource pool, assembling the right IT security team with the required skill set can be challenging.
However, it’s of the utmost importance to build the right team to implement and manage your network (deploy tools, network threat monitoring, incident handling, etc.). It’s just as important to provide them with the necessary training to upgrade and cultivate their skills continually.
In Summary
The threat landscape is continuously evolving and, therefore, security must be agile. For instance, defense in depth, where security controls were laid out in layers (akin to the layers of an onion,) is no longer considered sufficient to protect the IT infrastructure. Instead, a defense in breadth model — where multiple controls are deployed at every layer of the open system interconnection (OSI) model — or a combination of the two approaches is considered more effective.
While there is no one proven technique for establishing a resilient network infrastructure, with any luck, the above recommendations on network security best practices will get you started in the right direction.























 (38 votes, average: 4.66 out of 5)
(38 votes, average: 4.66 out of 5)






No comments