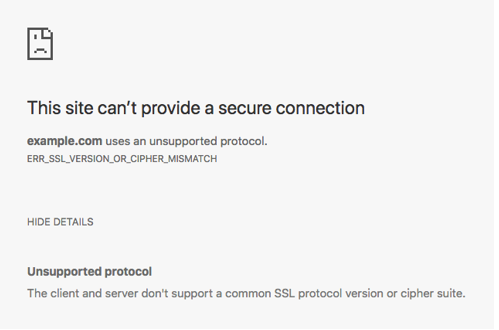
If you’re a website owner, the browser throwing an SSL certificate error message such as “ERR_SSL_VERSION_OR_CIPHER_MISMATCH” [CC1] does not help your business. It also doesn’t help to boost the confidence of your end-users, especially in the current cyber landscape.
What ERR_SSL_VERSION_OR_CIPHER_MISMATCH Means
When a user receives this error message while trying to access your site, it means that your server and the visitor’s browser (client) are unable to establish a secure, encrypted connection due to an unsupported protocol. There are a few potential causes for this, but it’s typically because your SSL certificate is misconfigured.
The mantra that most security gurus are trying to drill into the collective consciousness of netizens is that “secure” doesn’t mean “safe.” The word on the street is that more than half of the super tech-savvy cybercriminals have already switched to HTTPS, and the green padlock with secure written all over it could be extremely misleading. The padlock merely denotes that the communication channel between your client’s browser and your web server will be encrypted. Whether the server is legit, or you’re being coaxed into heading over to a phishing website is something that can’t be determined with a green padlock (unless the web server has an EV SSL certificate) — hence, you might not be safe at all.
With the average internet user already at the edge of their seat due to increasing data breaches and cyber security threats, it is not a glorious moment when they visit your site and encounter an SSL error message. It’s of the utmost importance to fix these errors to avoid any adverse impact on business and to retain your customer’s trust.
Let’s discuss some of the scenarios which can cause the ERR_SSL_VERSION_OR_CIPHER_MISMATCH error and look at ways to fix it.
PositiveSSL EV Certificates from $79.84/year!
Get the lowest prices on trusted SSL/TLS certificates from Sectigo brands.
Shop for Sectigo SSL CertificatesTROUBLESHOOTING: ERR_SSL_VERSION_OR_CIPHER_MISMATCH
While this error is more commonly seen on older browsers or operating systems, that isn’t always the case — and the SSL certificate could also be responsible for it.
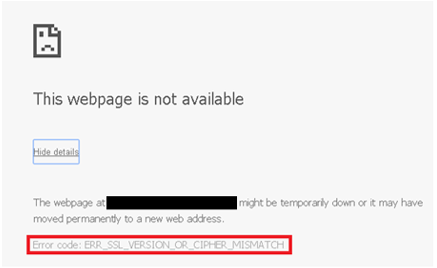
Other variations of the same error message include Error 113 and unsupported protocol errors as show in the images below:

- Run an SSL Certificate Check
The first step is to perform an SSL check on the certificate installed on the web server. You can use the free SSL Checker from Qualys SSL Labs, enter the hostname, and hit submit.
- See If There is a Certificate Name Mismatch
On the Qualys SSL Checker, this message will show up if the tool can recover a certificate for the site but if the domain names listed on the certificate do not match your queried domain. According to the Qualys report, a mismatch could happen due to any of the following scenarios:
- The site shares an IP address with some other site that uses SSL.
- The website no longer exists.
- The domain points to the old IP address which hosts some other site.
- The site uses a content delivery network (CDN) that doesn’t support SSL.
- The domain name alias was not included in the certificate.
You can also view the certificate information to see if it matches with the current site you’re on.
- Determine Whether the Site Is Running an Old Version of TLS
Ideally, the TLS version on the webserver should be 1.2 or higher (preferably TLS 1.3). On the Qualys SSL Checker tool under the configuration tab, you can see the current version of TLS running on the server. For older versions, you can reach out to the host and ask them to update their TLS version.
- Consider the Cause May Be an Outdated OS
The latest SSL certificates are not compatible with old operating systems (OS). Browsers also withdraw support for newer technologies on old operating systems. For instance, Chrome withdrew support for Windows XP in 2015.
- See If the Site is Running an Outdated RC4 Cipher Suite
The current cipher suite can be seen on the Qualys SSL Checker tool. Ensure that the server configuration is enabled with a different cipher suite than RC4. Not only is RC4 not pseudo-random in the generation of the keystream and has keystream biases but also the key scheduling algorithm is extremely weak.
Chrome removed support for RC4 Cipher Suites from version 48 and upwards. Google and Mozilla’s deprecation of RC4 cipher suite is the leading cause of this error. In the case of large enterprise deployments that use RC4, they might be resistant to change their configurations since it takes longer to process and implement changes in a complex environment.
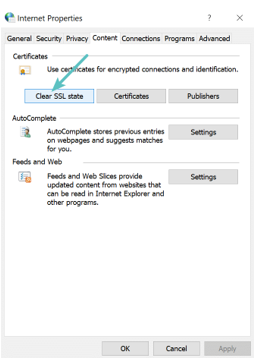
- Users Can Clear Their SSL State
Similar to clearing browser cache, clearing the SSL state takes care of any synchronization issues. On Chrome:
- Open Proxy Settings.
- In the Internet Properties window, go to the Content tab and click on Clear SSL State.
- Click OK and restart your browser.
- Temporarily Disable Your Antivirus
Some antiviruses get their certificates in the mix and create confusion by adding a layer between the browser and the server. If none of the above-mentioned fixes work, as a last resort, users can try disabling the antivirus temporarily. This can sometimes fix the issue. However, we don’t recommend this action because it leaves you vulnerable to cyberattacks. If you choose to perform this step, proceed with caution.
- Check Whether the Website Is Available Over HTTP
Try to reach the website over HTTP instead of using HTTPS. If you don’t receive the same error, the issue needs to be fixed at the server end.
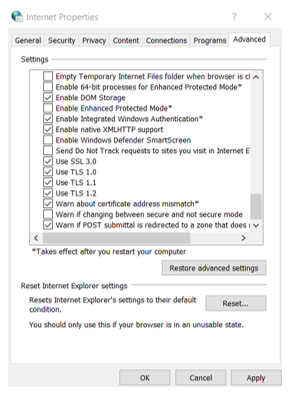
- Enable All SSL/TLS Versions
- On Chrome, open Settings and search for proxy settings in the search field.
- Open Proxy Settings and in the Internet Properties window click on the Advanced tab.
- Enable all the versions of SSL/TLS.
- Disable QUIC
On the Chrome browser, go to chrome://flags, and search for “experimental QUIC protocol” in the search field. If enabled, disable this setting and restart the browser. Firefox does not yet support QUIC.
We hope one of the above fixes worked wonders for you, and you can now access the website without any pesky error messages ruining your browsing experience.
Encryption Resources
- Hashing vs Encryption — The Big Players of the Cyber Security World
- SSL vs TLS: Decoding the Difference Between SSL and TLS
- IP Leak Test — Quick Tips to Check Whether Your IP Is Leaking
- Comodo CA is now Sectigo: FAQs
- 5 Differences Between Symmetric vs Asymmetric Encryption
- What Is Asymmetric Encryption & How Does It Work?

 (34 votes, average: 4.88 out of 5)
(34 votes, average: 4.88 out of 5)