Even though personal and business email communications are commonplace today, it continues to be one of the most vulnerable platforms in terms of security. Email security is a major concern for most businesses, as it’s often the weak point in their digital infrastructure. Some common email threats include eavesdropping, delivering malware through emails, address spoofing, phishing, etc.
People continue to fall prey to these attacks and spam, with technology not being able to filter out every scam email. It is, therefore, of utmost importance that we actively participate in ensuring secure email communication. S/MIME certificates (sometimes written as “S Mime certificates”) are a step in the right direction. With a Sectigo S/MIME certificate, for example, you can sign all your emails and encrypt them both in storage and in transit. In addition to securing your data at all times, this certificate also ensures that no one can impersonate you because your emails are digitally signed.
Let’s take a closer look at what an S/MIME certificate is and how it works.
What Is S/MIME Certificate?
RSA Data Security initially developed S/MIME, or what’s also known as secure/multipurpose internet mail extensions. It’s a protocol standard defined by the Internet Engineering Task Force (IETF) that enhances email security by allowing you to encrypt MIME data, aka emails.
Key Features of SMIME Certificate
- Industry-standard for public key encryption (asymmetric encryption) for MIME-based data.
- Offers two key email security functionalities — digital signatures and encryption.
- Digital signatures provide message integrity, authentication, and non-repudiation.
- Encryption provides data confidentiality (both for in-transit and at-rest data).
Because S/MIME uses asymmetric public key infrastructure (PKI), it employs two keys mathematically associated with each other to facilitates email security. By digitally signing your emails, the intended recipient can verify that the message was actually sent by you and hasn’t been tampered with or modified. When the email is en route from your computer to the recipient’s device, data encryption ensures that any attacker over the wire can’t read the contents of the message.
An SSL/TLS certificate installed on your email provider’s helps to facilitate a secure communication channel between you and your email server. However, it doesn’t encrypt your stored or archived emails, nor does it encrypt your emails in transit from other servers. Using an S/MIME certificate on client agents does away with both these drawbacks. Note that while SSL/TLS certificates are installed on servers, S/MIME certificates are installed on clients. Sectigo’s S/MIME certificates can be automatically deployed through a zero-touch deployment method into all mail clients.
Buy Sectigo Email S/MIME Certificate – Save 21%
Save 21% on Sectigo Email S/MIME Certificate. It ensures message integrity and helps you to set up DMARC.
How Does an S/MIME Certificate Work?
We mentioned earlier that S/MIME certificates utilize asymmetric encryption. The graphic below illustrates how asymmetric encryption works to encrypt and decrypt plaintext information.
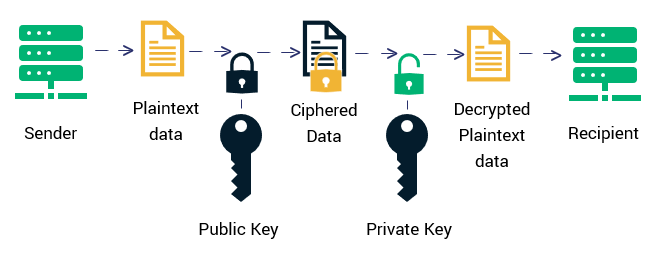
Let’s understand how asymmetric encryption works using an example.
Consider that Ben wants to send an email to his friend Jerry but does not want anyone else on the network to read or modify it. Ben uses Jerry’s public key to encrypt the message. Anyone can have access to this public key. Therefore, Ben or anyone can encrypt the message they want to send to Jerry. An intruder on the network cannot make sense of this message, though, without the corresponding private key. The private key is only accessible to Jerry, so only he can decrypt and read the message. You can get an email signing certificate from a trusted certificate authority (CA) and use this to digitally sign your messages (the certificate is automatically attached to the mail) before sending it off. The way this works is as follows:
- A digital signature is associated with two keys, a private key, and a public key.
- Authentication is done using the public key, whereas the private key is used to generate the signature itself.
- The public key is sent along with every protected email message to assert the identity of the sender.
- The private key, on the other hand, generates and applies the unique digital signature to each email. Signatures verify that the message is unaltered and not tampered by an unauthorized third-party.

 (42 votes, average: 4.74 out of 5)
(42 votes, average: 4.74 out of 5)